In response to IBM’s Value of a Knowledge Breach 2025 report, the typical price of a company knowledge breach in the USA was $10.22 million, up 9 p.c from 2024, as a consequence of increased regulatory fines and detection and escalation prices. Knowledge breaches disrupt operations, usually leading to lack of knowledge, hurt to organizational repute, fines, and important prices to revive techniques and get well.
Knowledge breaches remind us of the significance of cyber resilience as a vital ingredient of survivability and continuity of operations for all organizations, particularly these working mission-essential techniques, high-value techniques, and/or essential belongings. Resilience can be essential to decreasing the prices related to safety breaches in addition to minimizing injury to mission-essential techniques attributable to adversarial occasions. This submit highlights an strategy to utilizing knowledge analytics as a “power multiplier” for cyber resilience, and it suggests greatest practices to assist organizations achieve situational consciousness on their present safety posture. It additionally gives steerage for tailoring resilience efforts to boost a corporation’s skill to anticipate, stand up to, get well from, and adapt to evolving threats.
A Sensible Method to Cyber Resilience
Cybersecurity is commonly considered retaining the attackers out or just stopping an assault. Framing the issue in all-or-nothing phrases accepts unbounded danger and consequence as soon as a boundary is breached. A resilience-focused strategy helps organizations develop the power to anticipate, stand up to, get well from, and adapt to adversarial occasions. Normal practices akin to configuring safety settings, enterprise periodic vulnerability scans, and well timed patch administration tackle apparent weaknesses. However these measures alone don’t represent a enough or unified strategy to cybersecurity. An inconsistent implementation of safety controls usually requires safety directors to depend on expertise over formal steerage in addition to cycles of preparation pushed by inspections or audits. Organizational leaders ought to as a substitute work to develop a structured hardening framework to push safety efforts towards a constant, proactive strategy. This weblog submit illustrates how a various array of present tips and sources might be dropped at bear to boost resilience.
The Protection Data Programs Company (DISA) has revealed Safety Technical Implementation Guides (STIGs) and Safety Requirement Guides (SRGs), These present an vital step to handle the hole. The STIGs present detailed steerage for the configuration of purposes, databases, working techniques, and community gadgets, whereas SRGs deal with safety requirement frameworks that align to federal requirements. Each STIGs and SRGs are publicly out there sources which have a management mapping construction aligning with NIST SP 800-53 Safety and Privateness Controls for Data Programs and Group and NIST SP 800-171 Defending Managed Unclassified Data in Nonfederal Programs and Organizations. Whereas designed for the Division of Conflict, these guides will help any group develop a measurable and standardized safety posture.
Cyber Resilience Implementation: An Organizational Case Research
On this case examine, a corporation liable for managing and sustaining essential infrastructure techniques has been using their asset stock to establish relevant STIGs and SRGS. For functions of this instance, they use the next {hardware} and software program and related STIGs and SRGs:
| {Hardware}/Software program | Required STIG/SRG Title |
|---|---|
| Home windows 11 | Microsoft Home windows 11 STIG |
| Mozilla Firefox Browser | Mozilla Firefox STIG |
| Microsoft Defender Endpoint | Microsoft Defender for Endpoint STIG |
| Juniper Router | Juniper Router STIG |
| Home windows Defender Firewall | Home windows Defender Firewall with Superior Safety STIG |
| Intrusion Detection and Prevention System | Intrusion Detection and Prevention System SRG |
| Digital Non-public Community (VPN) | Digital Non-public Community (VPN) SRG |
| Community Coverage | Community Infrastructure Coverage STIG |
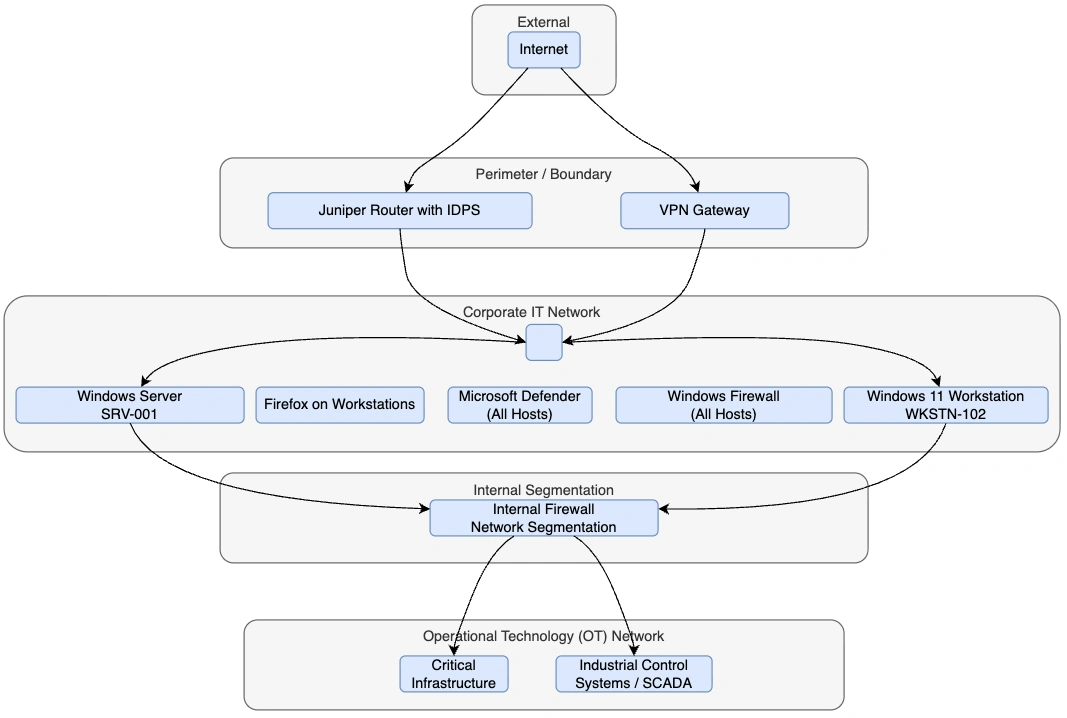
Determine 1: This determine particulars a high-level cybersecurity and community structure for the group, displaying how the completely different techniques are linked and guarded throughout layers.
The group downloaded the required STIGs and SRGs from the official DoW Cyber Alternate. Moreover, they downloaded the Safety Content material Automation Protocol (SCAP) Compliance Checker and STIG Viewer utility from the identical web site.
- STIG Viewer Software permits customers to view and handle the STIG and SRG checklists to evaluate and implement safety controls, analyze compliance, and doc findings.
- The Safety Content material Automation Protocol (SCAP) is a collection of “interoperable specs for the standardized expression, alternate, and processing of safety configuration and vulnerability info. SCAP permits constant automation and reporting throughout merchandise and environments by defining machine-readable content material and related processing necessities.”
After putting in the SCAP Compliance Checker, the group’s Data System Safety Officer (ISSO) and members of the safety staff created a brand new scan, importing the STIG and SRG information earlier than deciding on the right safety profile. The scan is a standardized technique to verify techniques based mostly on compliance with safety configurations, recognized vulnerabilities, and coverage violations. The safety profile choice choice assists in selecting which guidelines are scanned and consists of full compliance scanning and tailor-made variations based mostly on system classifications.
As soon as accomplished, the safety staff saved the outcomes of the scan as a .ckl file to simply import it into STIG Viewer. With the software, the ISSO might now view compliance failures inside the system and the severity of the failure related to the STIG or SRG rule. Moreover, the scan gives a standing indicator for every discovering to sign whether or not the scan was profitable, if the system is in compliance, or if the discovering was not reviewed. Some findings are usually not routinely reviewed and required guide evaluation by the system directors, which was completed by reviewing the documentation within the STIG or SRG that features the verify directions for assessing compliance.
As soon as the STIGs and SRGs have been mapped to the asset stock and the evaluation was accomplished, the artifacts have been built-in into an operational dashboard with system criticality rankings, compliance knowledge, and patch metrics. The Middle for Web Safety (CIS) Important Safety Controls V7 Measures and Metrics information is a sensible useful resource that gives greater than 100 actionable metrics in addition to benchmark targets and step-by-step steerage to assist organizations measure and enhance patch administration and SCAP-based vulnerability administration. The safety staff was capable of analyze this knowledge to trace deviations whereas additionally permitting safety architects to outline baseline configurations in live performance with the group’s cybersecurity technique. Moreover, hardened photographs of endpoints and servers have been created based mostly on the STIG findings and implementation steerage. These photographs allow baseline consistency throughout gadgets through the use of the preconfigured system photographs. Additionally they enable the safety staff to start out with an already permitted hardened baseline system when including new techniques, as a substitute of ranging from scratch.
Whereas this strategy creates a robust safety basis, it lacks enough knowledge to establish tendencies and areas of elevated danger. As historic STIG compliance knowledge accumulates, the safety staff is ready to strengthen enterprise safety by making use of advanced analytics to allow extra proactive identification and mitigation of dangers. On the diagnostic stage, the staff identifies root causes of configuration drift by correlating recurring misconfigurations, akin to failures, to implement baseline settings (e.g., disabled audit logging or unauthorized entry management configuration modifications) with change logs and deployment pipelines (i.e., the processes used to construct, check, and launch system updates). These diagnostic analytics enable the staff to transition to predictive analytics, forecasting future danger launched by inconsistent picture administration and undocumented administrative overrides.
Moreover, the safety staff was capable of mix STIG and SRG non-compliance severity utilizing the CAT ranges severity classification system:
- CAT I represents the best danger vulnerabilities (essential).
- CAT II signifies average danger.
- CAT III displays decrease danger findings.
Use of the CAT ranges, when mixed with CISA’s Recognized Exploited Vulnerabilities (KEV) catalog and asset publicity knowledge, ends in a weighted danger scoring mannequin. The safety staff found that solely a small proportion of techniques accounted for almost all of danger. The group was then capable of prioritize hardening, monitoring, and segmentation efforts based mostly on predicted chance and enterprise influence reasonably than responding to alerts after compromise makes an attempt.
As these processes matured, the group developed to extra proactive resilience engineering by mapping high-risk STIG and SRG failures to MITRE ATT&CK methods. This observe recognized how configuration weaknesses influenced danger whereas additionally enabling attack-path modeling and lateral motion likelihood. This perception allowed the group to make focused enhancements to authentication controls, privilege boundaries, and logging requirements to scale back the assault paths to essential belongings.
Subsequent Steps: Maturing Organizational Analytics Capabilities
As illustrated by our case examine, the applying of information analytics considerably improves resilience and survivability by enabling organizational leaders to make selections based mostly on knowledge and knowledge analytics. The sorts of analytics embrace descriptive analytics (understanding what has occurred), diagnostic analytics (explaining why it occurred), predictive analytics (anticipating what’s prone to occur), and prescriptive analytics (recommending what actions ought to be taken). As a corporation’s analytics functionality matures, it will possibly scale back and higher outline accepted danger.
Via the structured use of STIGs and SRGs mixed with data-driven analytics, the organizational leaders have been capable of transition from reactive compliance administration to a measurable, intelligence-driven resilience technique able to predicting threats by figuring out weaknesses earlier than they are often exploited and establishing preemptive commonplace actions. A key a part of any resilience technique includes knowledge that’s correct, well timed, and capable of instantly inform danger postures (e.g., asset criticality, vulnerability severity, publicity, and configuration drift).
A cyber resilience technique that focuses on refining knowledge analytics and allocating sources based mostly on the best danger permits organizations, particularly in resource-constrained environments, to maximise the influence of safety efforts whereas effectively using sources. This strategy means transferring resiliency additional left within the course of by prioritizing resilience in design selections and operational planning and permitting groups to behave proactively reasonably than reactively. It additionally permits quicker detection of adversarial occasions whereas growing the effectiveness of response actions, leading to fewer cascade failures, lowered downtime, and decrease prices related to an incident.

