Implementing DevSecOps can enhance a number of elements of the effectiveness of a software program group and the standard of the software program for which it’s accountable. Implementation of DevSecOps is a fancy course of, nevertheless, and the way in which a program evaluates progress in its DevSecOps implementation is vital. We suggest right here a body of reference for DevSecOps maturity, enabling organizations to give attention to outcomes – worth delivered – with out extreme give attention to compliance.
The Division of Protection’s (DoD) DevSecOps Documentation Set emphasizes program actions that pace supply, tighten safety, and enhance collaboration throughout the software program improvement lifecycle. However and not using a deep understanding of the interdependencies between the roles and actions inside a DevSecOps ecosystem, much less useful sub-activities may very well be optimized on the expense of others that is likely to be extra useful, leading to waste. Efficient DevSecOps ecosystems have to be primarily based on goal observations and information that account for the journey a software program program undergoes because it implements and improves its DevSecOps capabilities.
Evaluating DevSecOps implementation actions in opposition to a set of traits, attributes, indicators, and patterns in not enough. It have to be finished inside the context of worth delivered. Due to this fact, on this weblog put up, we first outline worth in a DevSecOps context. Subsequent, we describe how the DevSecOps Platform Impartial Mannequin (PIM) gives an authoritative reference mannequin for evaluating a company’s DevSecOps functionality maturity. Lastly, we offer a benchmark instance of a DevSecOps functionality profile.
What Is a Maturity Mannequin?
A maturity mannequin is an recognized set of traits, attributes, indicators, and patterns that characterize development and achievement in a specific area or self-discipline. It permits a company, resembling a software program manufacturing unit, to evaluate its practices, processes, and strategies in opposition to a clearly outlined benchmark. A scale of functionality maturity ranges might be established as an evolutionary scale that defines measurable distinctions from one stage of functionality to a different. Maturity fashions can be utilized to:
- Decide a company’s present stage of functionality after which apply these strategies over time to drive enhancements
- Decide how nicely a company is performing relative to others by inspecting the capabilities of peer organizations
It is crucial for organizations to carry out evaluations with worth in thoughts, as the worth proposition is required to outline the scope and perspective of a DevSecOps functionality evaluation.
Understanding Worth inside a DevSecOps Perspective
The apply of DevSecOps equips folks in a company with the instruments and processes essential to ship worth within the type of working and safe software program to customers rapidly and reliably. It requires that the group undertake a tradition and organizational construction aligned with Agile and Lean ideas.
Worth is basically measured by mission impression—how and the way a lot do the software program merchandise that the workforce delivers impression the aptitude and effectiveness of efficiency of a mission set? A consequence of this definition is that worth can’t be realized till the product is not only delivered and deployed but in addition used to finish missions. DevSecOps is due to this fact structured to not cease at supply or deployment, however moderately to proceed via operations – and to loop again to improvement in order that the software program advantages from suggestions from actual customers on actual missions. See Determine 1.

Determine 1: DevSecOps is a steady loop.
How Worth Drives Scope
DevSecOps shouldn’t be one thing you purchase; it’s one thing that a company (or enterprise) is. It embodies the guiding ideas of Agile and Lean software program improvement. DevSecOps combines group context and tradition with practices and instruments:
- Enterprise Mission: captures stakeholder wants and channels the entire program in assembly these wants. It solutions the questions Why and For Whom the enterprise exists.
- Functionality to Ship Worth: covers the folks, processes, and know-how essential to construct, deploy, and function the enterprise’s merchandise.
- Merchandise: the items of worth delivered by this system. Merchandise make the most of the capabilities delivered by the software program manufacturing unit and operational environments.
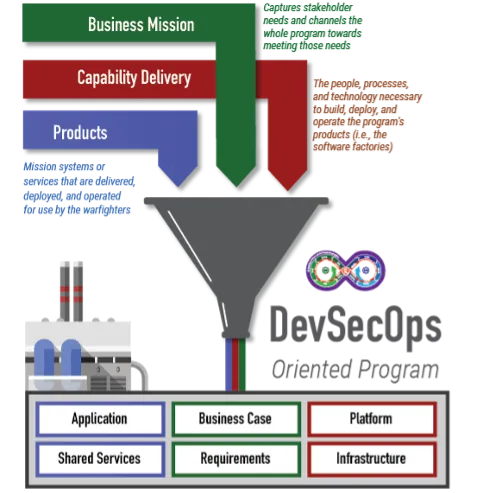
Determine 2: DevSecOps is an built-in enterprise.
All these elements have to be introduced collectively right into a single group, ideally below a single DevSecOps product proprietor, with the give attention to delivering worthwhile merchandise to the person neighborhood. It might not be attainable for the DevSecOps product proprietor to personal all groups and processes essential to ship worth; nevertheless, it’s crucial that they personal the complete end-to-end strategy of delivering that worth. Lean practices might help allow a DevSecOps product proprietor to extra readily determine wasteful, redundant, and in any other case pointless duties within the present set of processes and optimize those who stay. Even when they can’t absolutely management exterior stakeholders, they’re finest positioned to mitigate the impacts of inefficiency in these processes by optimizing and realigning the processes that they do management. For instance, a company should observe an exterior approval course of earlier than the recipient can set up and function a delivered utility. If this course of is expensive or takes per week or extra, and the product proprietor can’t at present optimize that timeframe, the product proprietor might as an alternative determine to scale back the frequency of supply and lengthen the event cycle in order that delivered software program has an opportunity to get via that approval course of, get put in, and get suggestions to the event groups earlier than the subsequent scheduled supply. This alignment of frequency of supply to operational acceptance price is essential to optimize stream, however solely a stakeholder with perception into your complete course of can acknowledge this and adapt.
How Functionality Evolves
What DevSecOps brings to the desk is the automation to enhance the agility and high quality of software program in a method that’s repeatable, predictable, dependable, well timed, and safe. As proven in Determine 3 beneath, that is an iterative course of. DevSecOps incorporates automation to streamline processes, carry out repeated duties, full duties quicker, and scale back human error. Automation, nevertheless, first requires a well-defined set of processes that the groups can persistently and reliably execute and which have demonstrated worth. In truth, a well-defined but solely handbook course of is most popular to an ill-defined and absolutely automated course of.
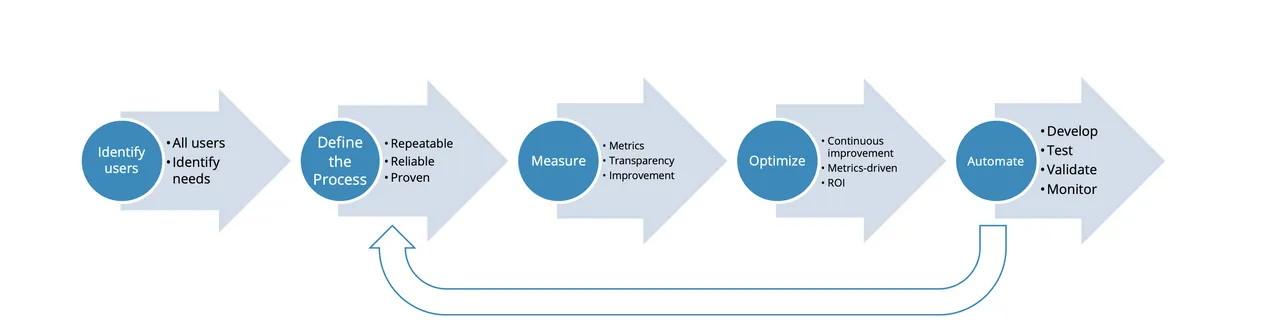
Determine 3: Course of automation and optimization loop.
The important thing components of defining good course of are as follows:
- Establish customers. Who’s the method for, and what’s worthwhile for them? The method have to be oriented to their wants.
- Outline the method. Doc a dependable and repeatable set of steps, develop checklists, and use a service desk or ticketing system to implement a easy workflow to seize situations of the method, their progress, and points regarding them. No automation is required right here, however it is very important be certain that the method is executed the identical each time and a system for capturing metrics is in place.
- Measure. Watch as the method is executed and determine ache factors and different areas for enchancment.
- Optimize. Incrementally enhance the method till it’s dependable and repeatable.
- Automate. As soon as sufficient information is accessible, decide the processes which have a excessive sufficient return on funding (ROI) to automate and implement automations.
It is very important perceive that to justify automation there have to be an anticipated price of return that, unfold over an affordable time frame, is greater than the price to automate. Determine 4 beneath illustrates the automation determination curve. To calculate the ROI, you could first have a repeatable course of in place and sufficient information from measuring it to know the advantages from automating it. That is why it is vital to not rush to implement automations earlier than the ROI image is absolutely understood. The pure evolution of DevSecOps practices and instruments is captured within the maturity ranges described beneath.
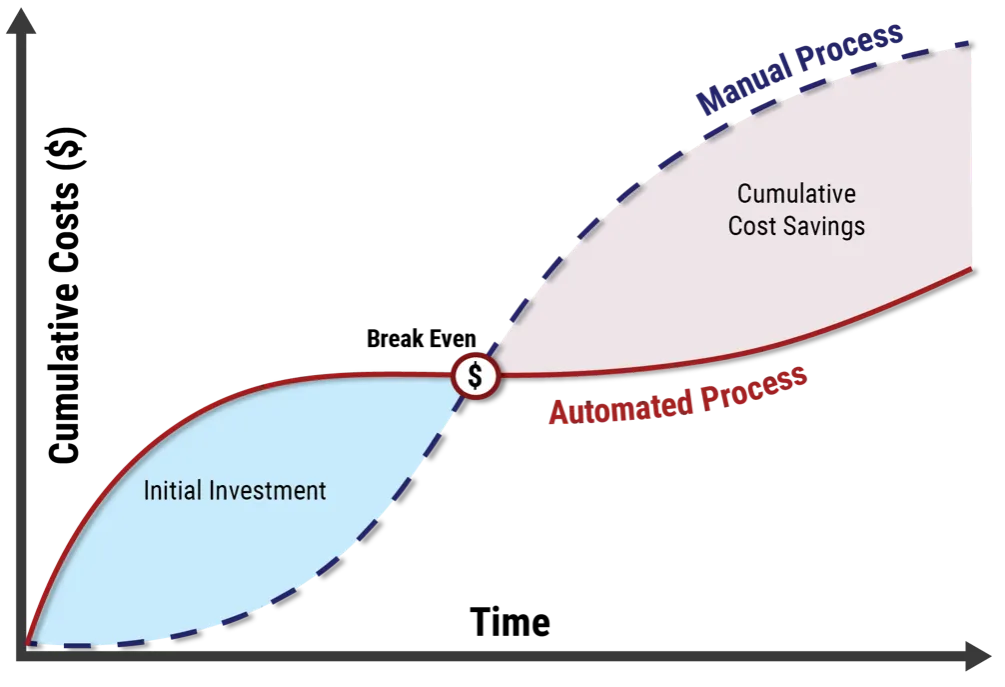
Determine 4: Automation ROI curve.
DevSecOps Platform Impartial Mannequin
The DevSecOps Platform Impartial Mannequin (PIM) is an complete reference to totally design and execute an built-in Agile and DevSecOps technique during which all stakeholder wants are addressed. It was developed utilizing model-based programs engineering (MBSE) methods to holistically outline the actions essential to consciously and predictably evolve the pipeline, whereas offering a proper method and methodology to constructing a safe pipeline tailor-made to a company’s particular necessities. The DevSecOps PIM features a four-level maturity mannequin that helps the mapping of present or proposed capabilities onto the set of capabilities and necessities outlined within the PIM. This alignment ensures that the DevSecOps ecosystem into consideration, or being assessed, implements the breadth of finest practices required to attain a given stage of maturity. The PIM defines 4 maturity ranges the place increased maturity ranges construct upon the practices of decrease maturity ranges. These maturity ranges are outlined as follows:
- ML1 – Carried out Fundamental Practices: This ML represents the minimal set of engineering, safety, and operational practices that’s required to start supporting a product below improvement, even when these practices are solely carried out in an advert hoc method with minimal automation, documentation, or course of maturity. This stage is concentrated on minimal improvement, safety, and operational hygiene.
- ML2 – Documented/Automated Intermediate Practices: Practices are accomplished along with assembly the ML1 practices. This stage represents the transition from handbook, advert hoc practices to the automated and constant execution of outlined processes. At this stage, the pipeline contains the aptitude to automate the practices which might be most frequently executed or produce essentially the most unpredictable outcomes. These practices embody establishing processes that permit actions to be repeated.
- ML3 – Managed Pipeline Execution: Along with performing the practices established below ML1 and ML2, practices at this stage embody persistently assembly the knowledge wants of all related stakeholders related to the product below improvement in order that they will make knowledgeable choices as work objects progress via an outlined course of.
- ML4 – Proactive Reviewing and Optimizing DevSecOps: Practices are accomplished along with assembly the extent 1-3 practices. At this stage, practices embody reviewing the effectiveness of the system in order that corrective actions are taken when essential and quantitively bettering the system’s efficiency because it pertains to the constant improvement and operation of the product below improvement.
The maturity mannequin considers the pure evolution of an excellent course of. ML1 focuses on defining the core processes to engineering, securing, and working software program. Organizations should first perceive their wants earlier than they will automate them. This isn’t to say there may be not automation at ML1, it’s merely targeted on the minimal set of practices one would anticipate to see with or with out automation. ML2 is concentrated on creating dependable and repeatable practices during which automation can play a key function. ML3 focuses on measurement and assembly varied data wants throughout a wide range of stakeholders, adopted by ML4 which is concentrated on optimization.
Along with maturity ranges, the DevSecOps PIM is damaged down into 10 capabilities:
-
Configuration administration is the set of actions used to ascertain and preserve the integrity of the system and product below improvement and related supporting artifacts all through their helpful lives. Totally different ranges of management are acceptable for various supporting artifacts and implementation parts and for various deadlines. For some supporting artifacts and implementation parts it could be enough to keep up model management of the artifact or factor that’s traced to a particular occasion of the system or product below improvement in use at a given time, previous or current, so that each one data associated to a given occasion, or model, is thought. In that case, all different variations of the artifacts and parts might be discarded as subsequent iterations are generated or up to date. Different supporting artifacts and implementation parts might require formal configuration, during which case baselines are outlined and established at predetermined factors within the lifecycle. Baselines and subsequent modifications, which can function the premise for future efforts, are formally reviewed and authorized. The configuration administration functionality of a system matures with elevated consistency and completeness of the integrity controls which might be put in place to seize all supporting artifacts and implementation parts related to the system and product below improvement whereas preserving tempo with the DevSecOps pipeline via automation and integration with all elements of the lifecycle. This contains (1) monitoring the connection between artifacts and parts for a given occasion, or model, of the system or product below improvement, (2) capturing enough data to determine and preserve configuration objects, even when those that created them are now not obtainable, (3) defining the extent of management every artifact and factor requires primarily based on technical and enterprise wants, (4) systematically controlling and monitoring modifications to configuration objects, and (5) imposing and logging of all required related stakeholder evaluations and approvals, primarily based on the group, challenge, and workforce insurance policies and procedures. -
Deployment is the set of processes associated to the supply or launch of the product below improvement into the setting during which customers of the product work together with it. The deployment capabilities of the system mature with elevated ranges of automation and superior rollback and launch performance. - Internet hosting providers are made up of the underlying infrastructure and platforms that each the system and product below improvement function upon. This contains the assorted cloud suppliers, on premises bare-metal and virtualization, networks, and different software program as a service (SaaS) that’s utilized together with the administration, configuration, entry management, possession, and personnel concerned.
- Integration is the method of merging modifications from a number of builders made to a single code base. Integration might be made manually on a periodic foundation, sometimes by a senior or lead engineer, or it may be made constantly by automated processes as particular person modifications are made to the code base. In both case, the aim of integration is to assemble a sequence of modifications, merge and deconflict them, construct the product, and be certain that it features as meant and that no change broke the entire product, even when these modifications labored in isolation.
- Monitor and management includes constantly monitoring actions, speaking standing, and taking corrective motion to proactively deal with points and persistently enhance efficiency. Extra mature tasks automate as a lot of this as attainable. Acceptable visibility allows well timed corrective motion to be taken when efficiency deviates considerably from what was anticipated. A deviation is critical if it precludes the challenge from assembly its targets when left unresolved. Gadgets that needs to be monitored embody value, schedule, effort, commitments, dangers, information, stakeholder involvement, corrective motion progress, and activity and work product attributes like measurement, complexity, weight, type, match, or operate.
-
Planning and monitoring is the set of practices one makes use of to outline duties and actions. It additionally contains the assets one must carry out these duties and actions, obtain an goal or dedication, and monitor progress (or lack thereof) in direction of attaining the given goal. It gives the mechanisms required to tell related stakeholders the place an effort at present is inside the course of and whether or not it’s on monitor to supply the anticipated outcomes. These mechanisms permit related stakeholders to find out what has been achieved and what changes or corrective actions must happen to account for impediments and different unexpected points. Ideally, impediments and points are proactively recognized and addressed. Practices embody documenting actions and breaking them down into actionable work to which one can assign assets, capturing dependence, forecasting, mapping work to necessities, accumulating information, monitoring progress to commitments, and reporting standing. The planning and monitoring functionality of a system matures because the automation and integration of related practices will increase. -
High quality assurance is a set of impartial actions (i.e., free from technical, managerial, and monetary influences, intentional or unintentional) designed to supply confidence to related stakeholders that the DevSecOps processes and instruments are acceptable for, and produce services and products of appropriate high quality for, their meant functions. It assumes that the group’s, workforce’s, and challenge’s insurance policies and procedures have been outlined primarily based on all related stakeholder wants, which can lead to a price stream that persistently produces services and products that meet all related stakeholder expectations. The standard assurance functionality of a system matures as its capacity to evaluate adherence to and the adequacy of the outlined insurance policies and procedures improves. - Software program assurance is the extent of confidence that software program features solely as meant and is free from vulnerabilities both deliberately or unintentionally designed or inserted as a part of the software program all through the complete software program lifecycle. It consists of two impartial however interrelated assertions:
- The software program features solely as meant. It displays solely performance meant by its design and doesn’t exhibit performance not meant.
- The software program is free from vulnerabilities, whether or not deliberately or unintentionally current within the software program, together with software program included into the ultimate system.
It’s the accountability of the DevSecOps system to make sure that software program that meets the group’s threshold for assurance is allowed to be deployed and operated. - Options improvement determines one of the simplest ways of satisfying the necessities to attain an end result. Its targets are to judge baseline necessities and various options to attain them, choose the optimum answer, and create a specification for the answer. Every improvement worth stream develops a number of options, that are merchandise, providers, or programs delivered to the client, whether or not inside or exterior to the enterprise.
- Verification and validation is the set of actions that gives proof that the system or utility below improvement has met anticipated necessities and standards. The scope contains the overall realm of testing, verifying, and validating actions and matures as automation, suggestions, and integration with different parts enhance.
These capabilities holistically incorporate the 200+ DevSecOps necessities wanted to attain the worth and mission impression illustrated within the DevSecOps steady loop above in Determine 1. Moreover, the PIM has outlined these capabilities when it comes to maturity. For instance, the PIM has outlined Planning & Monitoring Functionality Maturity stage 1 as Guide practices are used, with attainable use of some rudimentary instruments, that gather and retailer data used to trace and report standing and outputs from planning and monitoring actions.
Benchmarking Your DevSecOps Capabilities
Utilizing the DevSecOps PIM, an evaluation workforce can consider a company or program in opposition to the mannequin’s DevSecOps necessities by contemplating proof gathered, each within the type of written documentation and interviews, to find out the extent for every of the 200+ distinct necessities inside the PIM. Primarily based on DevSecOps assessments the SEI has carried out on quite a few organizations utilizing the PIM, we’ve got decided the next evaluation findings to be an efficient method to benchmark, or take a snapshot of, a company’s present DevSecOps maturity to ascertain a baseline and roadmap to steady enchancment. The 4 ranges of the dimensions of findings are:
- Persistently Demonstrated
- Sometimes Demonstrated
- Inadequate Proof Demonstrated
- Not Relevant
Utilizing this scale, one can produce a abstract benchmark resembling that proven in Determine 5.

Determine 5: Abstract of instance efficiency in opposition to the DevSecOps PIM necessities.
When specializing in worth, a key factor of the dimensions is Not Relevant. A requirement or exercise could also be known as out within the PIM as a finest apply in DevSecOps, however that doesn’t essentially imply it’s related to the group being assessed. If a given requirement inside the PIM doesn’t drive worth via mission impression, then it needs to be discarded as Not Relevant.
The DevSecOps PIM Maturity Mannequin can be utilized to
- present consciousness of what practices are already in place primarily based on a holistic set of Agile and DevSecOps necessities and determine practices that aren’t relevant
- determine ache factors, obstacles to collaboration, and technological obstacles with respect to DevSecOps and Agile ideas
- suggest areas of enchancment and technique relating to implementation of software program improvement instruments and methodologies that appear relevant to this system’s mission set
The objective of utilizing the DevSecOps PIM is to not set up a really perfect Agile or DevSecOps state. The objective is to determine actions that a company, and people of their orbit, can take to make assessments and, on this foundation, evolve right into a simpler and environment friendly group that delivers elevated worth for future engagements.

