Immediately’s methods are more and more software-intensive and complicated with a rising reliance on third-party expertise. By software program reuse, methods may be assembled quicker with much less growth price. Historically, methods had been primarily hardware-driven, and operational dangers had been primarily linked to reliability. Now methods are largely software-based. They don’t put on out like {hardware}, so crucial dangers are completely different. Software program parts nearly with out exception include vulnerabilities which are troublesome to handle straight. Inheritance of those vulnerabilities via the provision chain, as extra software program is acquired, will increase the administration challenges and magnifies the chance of potential compromise. As well as, we’ve got seen conditions the place suppliers unintentionally grow to be propagators of malware and ransomware (e.g., SolarWinds) via options that present computerized updates. Assaults on the software program provide chain (e.g., Shai-Hulud, a self-replicating worm) are more and more frequent and devastating.
The acquisition and operation of a system with efficient software program assurance requires efficient software program threat administration all through the lifecycle to determine and mitigate potential mission impacts. As detailed on this put up, via many years of expertise in working with packages throughout authorities and trade, our workforce of researchers in cybersecurity, acquisition, and system and software program engineering have recognized 5 foundational capabilities (pillars) that should be properly established to assist the acquisition of a system with efficient software program assurance: Software program Necessities, Software program Provide Chain Danger Administration, Software program High quality, System Integration, and Software program Metrics. These pillars tackle inconsistencies, errors, and disconnects in immediately’s software program administration that signify dangers to mission success. Cyber menace actors benefit from the obtainable gaps and potential errors in a system’s design, software program, {hardware}, firmware, and provide chain to bypass controls and leverage software program vulnerabilities of their assaults.
These gaps typically embrace improper assumptions about how protections will carry out when communications and knowledge sharing happen among the many varied software program and {hardware} parts of the system. There are additionally gaps within the management of contents of knowledge packets. Additional misunderstandings happen when designs are created for {hardware}, however the ensuing operate is dealt with by software program that will have inherent vulnerabilities. Complicated software program integrations are assembled from current parts and language libraries which are reused to carry out related actions however might not be constructed to specification. Moreover, reused parts might embrace sudden capabilities and assault surfaces that let unacceptable behaviors that attackers can leverage.
Present system threat evaluation approaches focus primarily throughout the boundaries of a system and encourage designing robust protections for crucial belongings, typically largely ignoring different elements of the system. Safety analysts typically ignore the function of software program in linking inner and exterior system parts. Attackers will leverage third-party software program, language libraries, open supply, and firmware as a conduit right into a goal system. Connections from exterior methods are one other avenue of threat. Assaults may be launched from much less protected however related methods, infrastructure, cloud and monitoring companies, and different trusted exterior sources. System sustainment processes resembling patching and expertise refresh may be one more technique of invading a goal system if efficient threat administration practices should not in place. The lag in implementation of each first-party and third-party software program updates to cut back vulnerabilities additional complicates the coordination throughout system parts, leaving gaps which are invaluable to attackers. Efficient implementation of processes and practices throughout the 5 pillars can mitigate these dangers.
Analysis Addressing Software program Assurance
The monetary influence from the exploitation of software program defects has grown from an estimated $60 billion influence yearly on the U.S. financial system in 2002 to the $26 billion-a-day world influence on immediately’s financial system, as famous by Yair Levy at a 2025 Cybersecurity Consciousness Month Lunch & Be taught, Webinar on the Middle for Data Safety, Schooling, and Analysis (CIPhER), Nova Southeastern College. Efforts to handle info safety threat are primarily based largely on ideas established in 1974 by Saltzer and Schroeder, however the expertise context at the moment was centralized mainframes, not the highly-distributed, networked, software-dependent present-day methods. Many of those unique ideas nonetheless maintain true, however they don’t tackle present facets of the operational context and the associated software program dangers. A broader set of ideas was revealed in 2013 by researchers on the SEI and College of Detroit Mercy to incorporate the more moderen challenges of assuring software program in a contemporary context as follows:
- Danger. A notion of threat drives assurance choices and uninformed organizations make poor threat decisions.
- Interactions. It’s now not enough to contemplate solely crucial belongings when every thing is extremely interconnected and efficient assurance requires that each one ranges and roles constantly acknowledge and reply to threat.
- Trusted dependencies. A lot of the software program depends on the peace of mind of software program parts within the provide chain, and the belief positioned in that assurance, which is outdoors the management of the unique software program’s stakeholders.
- Attacker. A broad group of attackers with rising expertise capabilities can compromise the confidentiality, integrity, and availability of any of a corporation’s expertise belongings.
- Coordination and training. Assurance requires efficient coordination amongst all expertise contributors.
- Nicely deliberate and dynamic. Assurance is without doubt one of the many facets of a system that should be traded off in opposition to different qualities (e.g., efficiency, security, reliability) and the realities of budgets and assets. The system should be fielded with enough assurance that’s aligned with, and permits for, efficient mission execution amid the realities of a extremely contested operational context.
- Measurable. Organizations with extra profitable assurance measures reply and get better quicker, study from assaults, and are higher ready to watch and detect potential issues. Efficient measures should be designed in and monitored to be helpful.
Acquisition lifecycle processes and practices for the administration of software-intensive methods should be enhanced to include these expanded ideas. As outlined under, the 5 pillars of software program assurance can present a stable base that helps this want. The planning and resourcing for these capabilities should be addressed early within the lifecycle in order that they’re in place for later choices about suppliers and the adoption of processes and practices for software program growth Our expertise has proven that delaying consideration of software program assurance and the 5 pillars till later within the lifecycle leads to expensive rework or the acceptance of weak software program assurance that places missions in danger.
Implementing Software program Assurance
Supply of a system with efficient software program assurance requires efficient software program administration to determine, monitor, and mitigate potential mission dangers. A variety of particular practices had been recognized and documented within the Acquisition Safety Framework revealed in 2024, however not each program wants each follow. The 5 key pillars outlined under can present a powerful foundation for establishing confidence that software program assurance has been addressed. Every of those focus areas must be extremely built-in into the acquisition lifecycle for a system to have the wanted constructing blocks for software program assurance. These are areas a program ought to already be addressing, however we’re seeing them insufficiently dealt with and continuously ignoring software program, resulting in gaps in software program administration that lead to insufficient software program assurance.
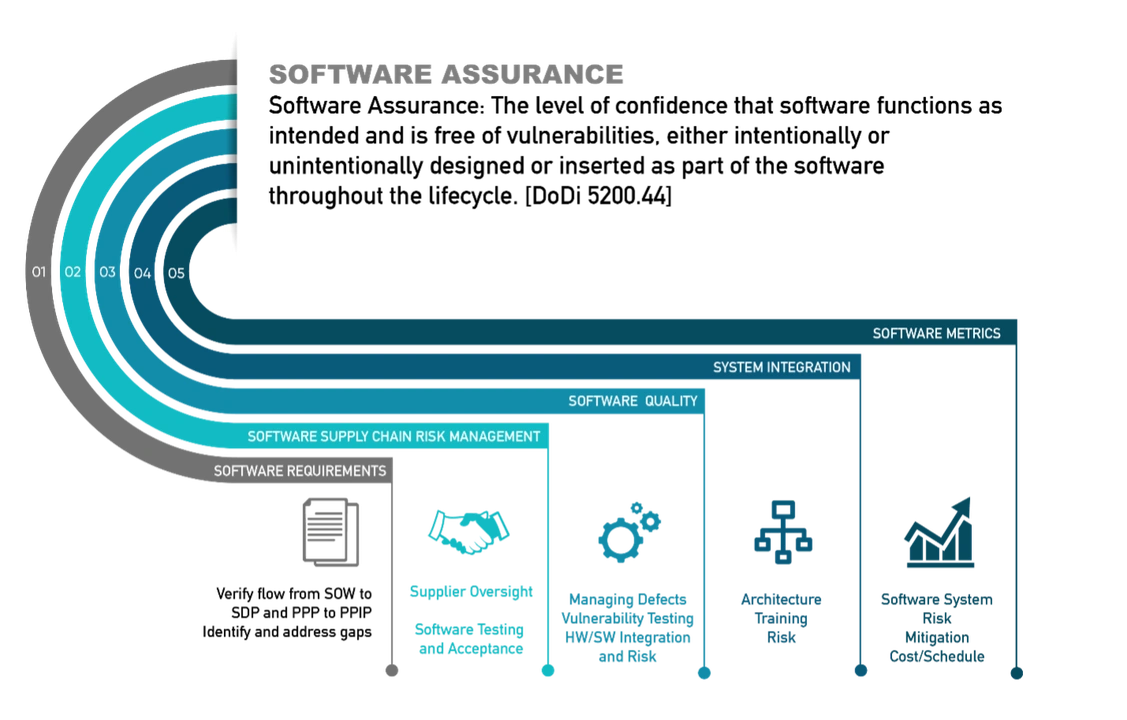
The primary pillar is Software program Necessities. That is outlined because the required performance assigned by the system design to the software program/firmware parts of the system to carry out their allotted capabilities inside acceptable constraints and high quality to assist the system mission. Inside a U.S. Division of Battle (DoW) acquisition, this info could be described at a excessive degree as a part of the assertion of labor (SOW). The contractor would offer a Software program Growth Plan (SDP) to explain how their system design would implement these necessities. Cybersecurity controls and different safety specs for the system could be additional described within the Program Safety Plan (PPP), and the contractor would describe how their system design addresses the PPP of their Program Safety Implementation Plan (PPIP). Necessities associated to software program assurance, software program high quality, software program provide chain administration, software program metrics, safety, and different qualities decided to be vital to software program assurance may be extracted from the SOW and mapped to the SDP and PPP to verify that the contractor’s plans for the delivered system will tackle the prescribed software program assurance wants. Additional steerage for addressing necessities is out there within the Safety Engineering Framework (SEF).
If the acquisition is following the key acquisition lifecycle, there are key evaluation factors the place contractor supply on these necessities may be monitored via their implementation of processes and practices wanted to construct, take a look at, and ship software program: System Necessities Evaluate (SRR), Preliminary Design Evaluate (PDR), and Vital Design Evaluate (CDR). Each software program buy and implementation ought to have related sorts of monitoring actions although they might not essentially be formal.
The second pillar is Software program Provide Chain Danger Administration. This pillar is outlined as governance and monitoring of individuals, processes, and expertise wanted to accumulate, handle, and maintain third-party software program/firmware to make sure it meets system necessities and mission wants all through its implementation. Use of third-party software program can supply important benefits in price and schedule, however it might probably additionally create cybersecurity and lifecycle dependency dangers that should be managed.
When deciding on a software program provider, it’s vital to think about how they tackle the software program assurance of their merchandise. As soon as a provider is chosen, Provide Chain Danger Administration ought to usually monitor provider merchandise to know when new vulnerabilities are found that pose a threat to the system. Fixed patching, expertise refresh integration, and different mitigation methods for vulnerability administration are a actuality of software program use that should be applied and managed throughout the lifecycle of all third-party software program. With software program it’s not potential to “set and neglect” the implementation till it wears out, however recognition of this want for fixed monitoring to determine dangers and mitigate them earlier than they’re realized will not be widespread. Monitoring inside an acquisition to make sure a specific provider is performing efficient threat administration of their suppliers can be crucial. To verify the contractor is successfully managing their suppliers, verification ought to be carried out in any respect key milestone evaluations.
A high-risk supply of third-party vulnerability is open supply software program (OSS), which GitHub estimates for use by 90 % of organizations and is valued at greater than $9 trillion. Dangers from these vulnerabilities are rising exponentially with the usage of synthetic intelligence (AI). Any software program acquired will probably include OSS, and the provider wants to handle these assurance dangers. The identification of acceptable open supply requires an acquisition to ascertain assurance standards earlier than allowing the software program for use. The Open Supply Software program Mission, Product, Safety, and Coverage report (OSS-P4/R) supplies a course of for outlining the choice standards and an automatic means for implementing the standards inside a software program integration pipeline. Out there on GitHub, it may be tailor-made for any group to implement their distinctive choice standards. OS-P4/R makes use of public knowledge sources and open supply instruments to assemble knowledge and knowledge correlated to provide chain considerations recognized by a selected acquisition.
The third pillar is Software program High quality. This pillar is outlined as constructing confidence that the folks, processes, and practices used to create and purchase software program are delivering wanted mission outcomes inside acceptable ranges of rigor and threat. Too typically high quality evaluations solely give attention to how properly the software program growth course of is carried out and don’t take a look at the precise high quality of the product that the method is delivering. Whereas course of high quality is vital, the supply of product high quality is what is going to in the end influence the extent of software program vulnerabilities and supply software program assurance enchancment. Software program metrics (see fifth pillar) will present indicators as to how properly the general software program high quality is dealt with. The sooner software program high quality gaps may be recognized and corrected, the much less influence there will likely be on price and schedule ought to high quality insufficiencies have to be addressed.
The fourth pillar is System Integration. IEEE defines integration (in ISO/IEC/IEEE 24748-6:2023(E) part 3.1.4 p. 2) as the method of mixing software program parts, {hardware} parts, or each into an general system. Every of those parts may be assured inside their growth. Moreover, the combination of those parts should be assured. That is achieved on the governance and system ranges, and inside growth and implementations groups. Software program experience is utilized to determine and tackle key software program assurance gaps in processes and practices all through the acquisition lifecycle. Milestone evaluations, acquisition technical evaluations, and choice factors are used to confirm that the coaching and practices are in place to assist software program assurance success.
The fifth, and last, pillar is Software program Metrics. That is outlined because the identification and evaluation of metrics to exhibit efficient lifecycle software program assurance to satisfy mission wants. On the product degree, there is usually a variety of metrics, similar to explicit high quality attributes of the system in growth and in addition course of attributes referring to the conduct of the engineering exercise. These metrics present goal knowledge to judge progress, course of, and high quality of delivered software program. You will need to acknowledge that there are attributes of a system or its engineering course of that could be important, however they’re troublesome to evaluate exactly. Regardless, efficient monitoring supplies a chance for early identification and correction of software program assurance gaps earlier than they influence price and schedule. With out this early monitoring, gaps are primarily found when the system is beneath a last analysis previous to implementation. At that time there may be little funding remaining to handle main software program assurance gaps, lots of that are the results of poor design choices. The acceptance of main software program assurance dangers jeopardizes operational functionality as a result of rising operational context described earlier.
Trying Forward: Understanding Software program Dangers and the Worth of Efficient Software program Assurance
The implementation of software program in immediately’s extremely contested operational setting mandates early and efficient software program administration processes and practices to ascertain efficient software program assurance. This won’t occur until the folks addressing system and software program design and implementation absolutely perceive the dangers posed by software program and the worth of efficient software program assurance. Efficient implementation of the 5 pillars of software program assurance will assist acquisitions within the identification, monitoring, and mitigation of software program assurance gaps.

