
The Sandworm Russian army cyber-espionage group is concentrating on Home windows customers in Ukraine with trojanized Microsoft Key Administration Service (KMS) activators and pretend Home windows updates.
These assaults doubtless began in late 2023 and have now been linked by EclecticIQ risk analysts with Sandworm hackers primarily based on overlapping infrastructure, constant Ways, Strategies and Procedures (TTPs), and continuously used ProtonMail accounts to register domains used within the assaults.
The attackers additionally used a BACKORDER loader to deploy DarkCrystal RAT (DcRAT) malware (utilized in earlier Sandworm assaults) and debug symbols referencing a Russian-language construct surroundings, additional reinforcing the researchers’ confidence that Russian army hackers had been concerned.
EclecticIQ recognized seven malware distribution campaigns tied to the identical malicious exercise cluster, every utilizing comparable lures and TTPs. Most not too long ago, on 12 January 2025, the analysts noticed the assaults infecting victims with the DcRAT distant entry Trojan in knowledge exfiltration assaults utilizing a typo-squatted area.
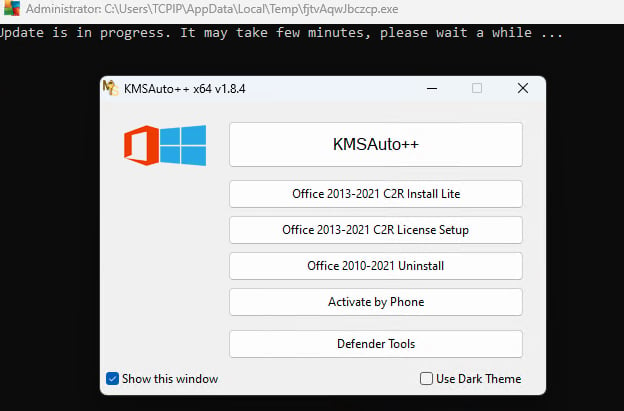
As soon as deployed on a sufferer’s system, the faux KMS activation device shows a faux Home windows activation interface, installs the malware loader, and disables Home windows Defender within the background earlier than delivering the ultimate RAT payload.
The assaults’ finish objective is to gather delicate info from contaminated computer systems and ship it to attacker-controlled servers. The malware steals keystrokes, browser cookies, browser historical past, saved credentials, FTP credentials, system info, and screenshots.
Sandworm’s use of malicious Home windows activators was doubtless prompted by the huge assault floor opened by the heavy use of pirated software program in Ukraine, which additionally plagues the nation’s authorities sector.
“Many customers, together with companies and important entities, have turned to pirated software program from untrusted sources, giving adversaries like Sandworm (APT44) a primary alternative to embed malware in extensively used applications,” EclecticIQ stated.
“This tactic allows large-scale espionage, knowledge theft, and community compromise, straight threatening Ukraine’s nationwide safety, crucial infrastructure, and personal sector resilience.”
Sandworm (additionally tracked as UAC-0113, APT44, and Seashell Blizzard) is a hacking group lively since no less than 2009 and a part of the Navy Unit 74455 of the Major Intelligence Directorate (GRU), Russia’s army intelligence service, primarily targeted on finishing up disruptive and harmful assaults concentrating on Ukraine.

