
A comparatively new ransomware operation named Interlock assaults organizations worldwide, taking the bizarre strategy of making an encryptor to focus on FreeBSD servers.
Launched on the finish of September 2024, Interlock has since claimed assaults on six organizations, publishing stolen knowledge on their knowledge leak web site after a ransom was not paid. One of many victims is Wayne County, Michigan, which suffered a cyberattack initially of October.
Not a lot is thought in regards to the ransomware operation, with a number of the first data coming from incident responder Simo in early October, who discovered a brand new backdoor [VirusTotal] deployed in an Interlock ransomware incident.
Quickly after, cybersecurity researcher MalwareHuntTeam discovered what was believed to be a Linux ELF encryptor [VirusTotal] for the Interlock operation. Sharing the pattern with BleepingComputer, we tried to check it on a digital machine, the place it instantly crashed.
Inspecting the strings inside the executable indicated that it was compiled particularly for FreeBSD, with the Linux “File” command additional confirming it was compiled on FreeBSD 10.4.
interlock.elf: ELF 64-bit LSB executable, x86-64, model 1 (SYSV), statically linked, BuildID[sha1]=c7f876806bf4d3ccafbf2252e77c2a7546c301e6, for FreeBSD 10.4, FreeBSD-style, not strippedNevertheless, even when testing the pattern on a FreeBSD digital machine, BleepingComputer was unable to get the pattern to correctly execute.
Whereas it is not uncommon to see Linux encryptors created to focus on VMware ESXi servers and digital machines, it’s uncommon to see ones created for FreeBSD. The one different ransomware operation recognized to have created FreeBSD encryptors is the now-defunct Hive ransomware operation, which was disrupted by the FBI in 2023.
This week, researchers from cybersecurity agency Pattern Micro shared on X that they discovered an extra pattern of the FreeBSD ELF encryptor [VirusTotal] and a pattern of the operation’s Home windows encryptor [VirusTotal].
Pattern Micro additional mentioned that the risk actors possible created a FreeBSD encryptor because the working system is usually utilized in important infrastructure, the place assaults could cause widespread disruption.
“Interlock targets FreeBSD because it’s broadly utilized in servers and significant infrastructure. Attackers can disrupt very important providers, demand hefty ransoms, and coerce victims into paying,” explains Pattern Micro.
The Interlock ransomware
Whereas BleepingComputer couldn’t get the FreeBSD encryptor working, the Home windows model ran and not using a downside on our digital machine.
In response to Pattern Micro, the Home windows encryptor will clear Home windows occasion logs, and if self-deletion is enabled, will use a DLL to delete the primary binary utilizing rundll32.exe.
When encrypting recordsdata, the ransomware will append the .interlock extension to all encrypted file names, and create a ransom word in every folder.
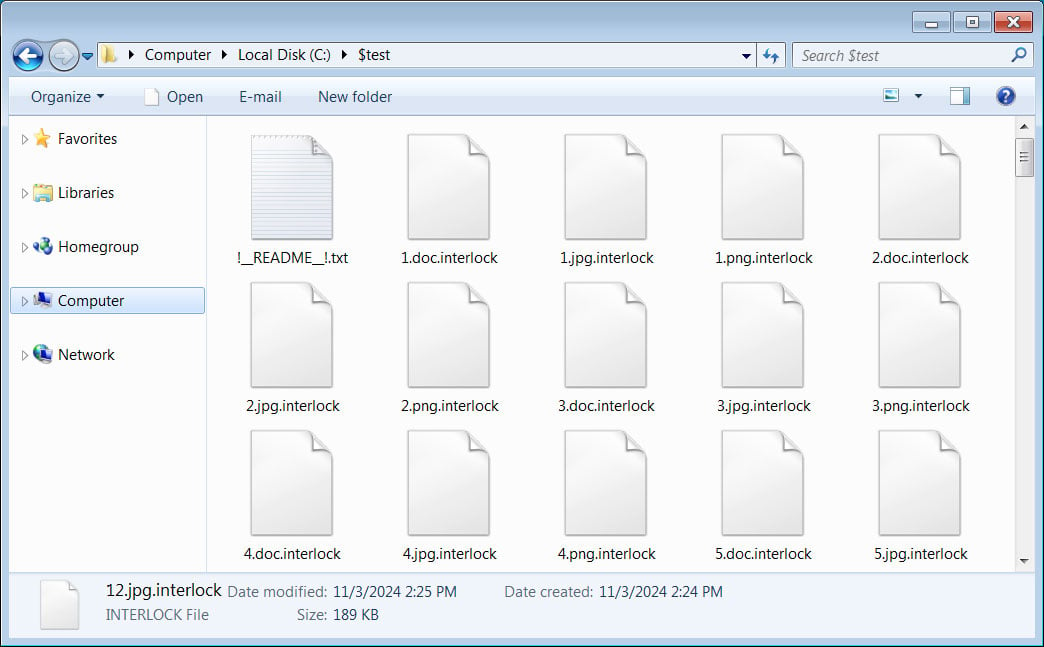
Supply: BleepingComputer
This ransom word is called !__README__!.txt and briefly describes what occurred to the sufferer’s recordsdata, makes threats, and hyperlinks to the Tor negotiation and knowledge leak websites.
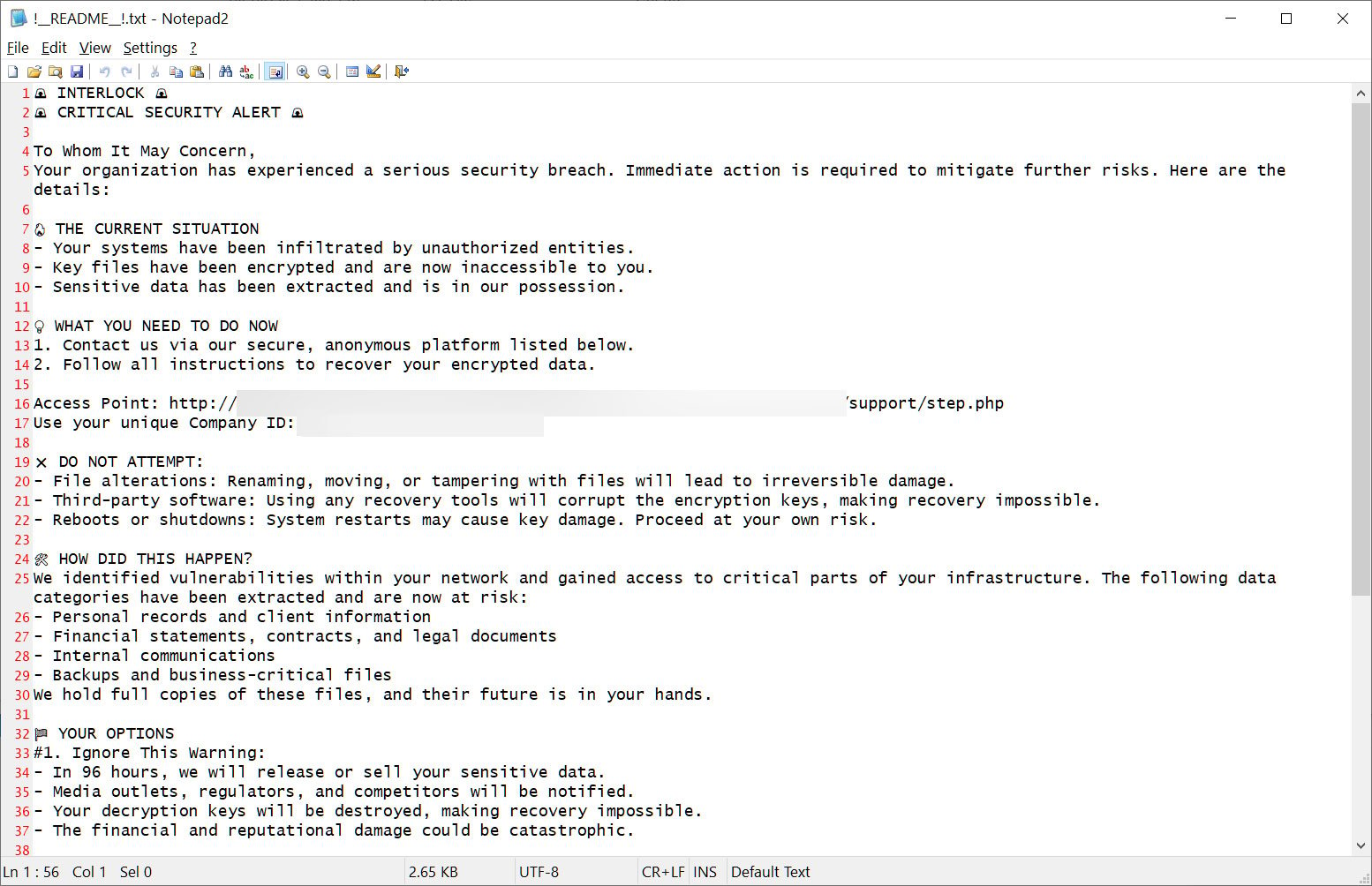
Supply: BleepingComputer
Every sufferer has a singular “Firm ID” that’s used together with an e-mail deal with to register on the risk actor’s Tor negotiation web site. Like many different current ransomware operations, the victim-facing negotiation web site simply features a chat system that can be utilized to speak with the risk actors.
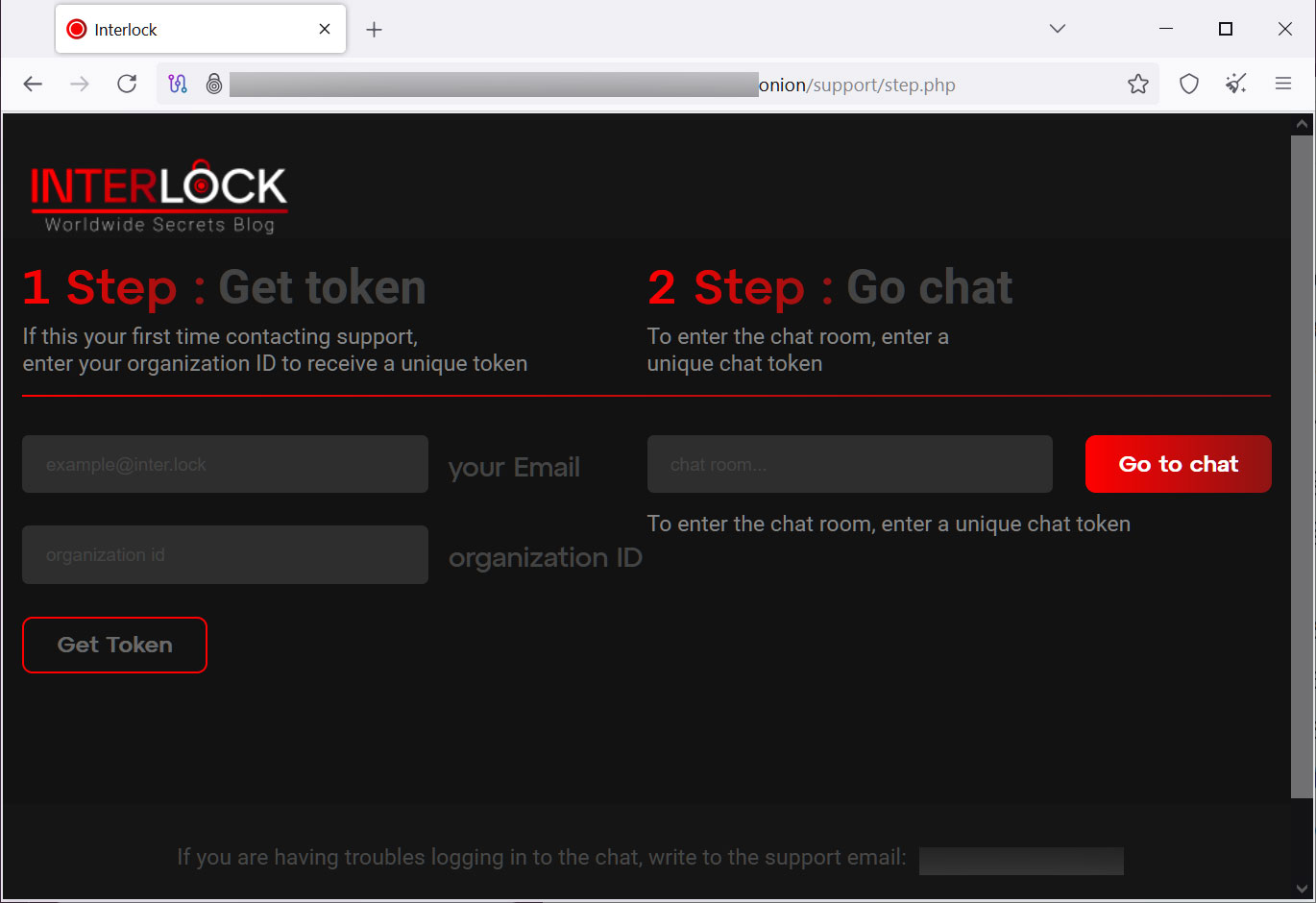
Supply: BleepingComputer
When conducting assaults, Interlock will breach a company community and steal knowledge from servers whereas spreading laterally to different units. When accomplished, the risk actors deploy the ransomware to encrypt the entire recordsdata on the community.
The stolen knowledge is used as a part of a double-extortion assault, the place the risk actors threaten to publicly leak it if a ransom will not be paid.
Supply: BleepingComputer
BleepingComputer has realized that the ransomware operation calls for ransoms starting from a whole bunch of hundreds of {dollars} to tens of millions, relying on the scale of the group.

