Software program is a rising part of right this moment’s mission-critical programs. As organizations develop into extra depending on software-driven expertise, safety and resilience dangers to their missions additionally improve. Managing these dangers is simply too typically deferred till after deployment because of competing priorities, comparable to satisfying price and schedule goals. Nonetheless, failure to handle these dangers early within the programs lifecycle cannot solely improve operational impression and mitigation prices, however it could additionally severely restrict administration choices.
For Division of Protection (DoD) weapon programs, it’s particularly vital to handle software program safety and resilience dangers. Proactively figuring out and correcting software program vulnerabilities and weaknesses minimizes the chance of cyber-attacks, weapons system failures, and different disruptions that might jeopardize DoD missions. The GAO has recognized software program and cybersecurity as persistent challenges throughout the portfolio of DoD weapon programs. To handle these challenges, acquisition applications ought to begin managing a system’s safety and resilience dangers early within the lifecycle and proceed all through the system’s lifespan.
This submit introduces the Safety Engineering Framework, an in depth schema of software-focused engineering practices that acquisition applications can use to handle safety and resilience dangers throughout the lifecycle of software-reliant programs.
Software program Assurance
Software program assurance is a degree of confidence that, all through its lifecycle, software program features as supposed and is freed from vulnerabilities, both deliberately or unintentionally designed or inserted as a part of the software program. Software program assurance is more and more vital to organizations throughout all sectors due to software program’s growing affect in mission-critical programs. Managing software program assurance is a problem due to the expansion in functionality, complexity, and interconnection amongst software-reliant programs.
For instance, think about how the scale of flight software program has elevated through the years. Between 1960 and 2000, the extent of general system performance that software program supplies to army plane pilots elevated from 8 p.c to 80 p.c. On the identical time, the scale of software program in army plane grew from 1,000 strains of code within the F-4A to 1.7 million strains of code (MLOC) within the F-22 and 8 million strains within the F-35. This pattern is anticipated to proceed over time. As software program exerts extra management over complicated programs (e.g., army plane), the potential threat posed by vulnerabilities will improve correspondingly.
Software program Defects and Vulnerabilities: A Lifecyle Perspective
Determine 1 beneath highlights the speed of defect introduction and identification throughout the lifecycle. This was derived from information introduced within the SEI report Reliability Validation and Enchancment Framework. Research of safety-critical programs, notably DoD avionics software program programs, present that 70 p.c of all errors are launched throughout necessities and structure design actions. Nonetheless, solely 20 p.c of the errors are discovered by the tip of code growth and unit take a look at, whereas 80.5 p.c of the errors are found at or after integration testing. The rework effort to appropriate necessities and design issues in later phases might be as excessive as 300 to 1,000 instances the hassle of in-phase correction. Even after the rework, undiscovered errors are prone to stay.

Determine 1: Fee of Defect Introduction and Identification throughout the Lifecycle
Given the complexities concerned in creating large-scale, software-reliant programs, it’s comprehensible that no software program is freed from dangers. Defects exist even within the highest high quality software program. For instance, best-in-class code can have as much as 600 defects per MLOC, whereas average-quality code usually has round 6,000 defects per MLOC, and a few of these defects are weaknesses that may result in vulnerabilities. Analysis signifies that roughly 5 p.c of software program defects are safety vulnerabilities. Because of this, best-in-class code can have as much as 30 vulnerabilities per MLOC. For average-quality code, the variety of safety vulnerabilities might be as excessive as 300 per MLOC. It is very important observe that the defect charges cited listed below are estimates that present common perception into the difficulty of code high quality and variety of vulnerabilities in code. Defect charges in particular initiatives can differ vastly. Nonetheless, these estimates spotlight the significance of lowering safety vulnerabilities in code throughout software program growth. Safe coding practices, code evaluations, and code evaluation instruments are vital methods to establish and proper recognized weaknesses and vulnerabilities in code.
As illustrated in Determine 1, safety and resilience should be managed throughout the lifecycle, beginning with the event of high-level system necessities via operations and sustainment (O&S). Program and system stakeholders ought to apply main practices for buying, engineering, and deploying safe and resilient software-reliant programs. In 2014, the SEI initiated an effort to doc main practices for managing safety and resilience dangers throughout the programs lifecycle, offering an strategy for constructing safety and resilience right into a system relatively than bolting them on after deployment. This effort produced a number of cybersecurity engineering options, most notably the Safety Engineering Threat Evaluation (SERA) methodology and the Acquisition Safety Framework (ASF). Late final 12 months, the SEI launched the Safety Engineering Framework.
Safety Engineering Framework (SEF)
The SEF is a group of software-focused engineering practices for managing safety and resilience dangers throughout the programs lifecycle, beginning with necessities definition and persevering with via O&S. It supplies a roadmap for constructing safety and resilience into software-reliant programs previous to deployment and sustaining these capabilities throughout O&S. The SEF builds on the foundational analysis of SERA and the ASF, offering in-depth steerage that elaborates on main engineering practices and learn how to carry out them.
SEF practices assist make sure that engineering processes, software program, and instruments are safe and resilient, thereby lowering the chance that attackers will disrupt program and system info and belongings. Acquisition applications can use the SEF to evaluate their present engineering practices and chart a course for enchancment, in the end lowering safety and resilience dangers in deployed software-reliant programs.
Safety and Resilience
At its core, the SEF is a risk-based framework that addresses each safety and resilience:
Threat administration supplies the muse for managing safety and resilience. In truth, threat administration strategies, instruments, and methods are used to handle each. Nonetheless, safety and resilience view threat from completely different views: Safety considers dangers from a safety standpoint, whereas resilience considers threat from a perspective of adapting to situations, stresses, assaults, and compromises. As proven in Determine 2, there may be some overlap between the chance views of safety and resilience. On the identical time, safety and resilience every have distinctive dangers and mitigations.
Determine 2: Threat Views: Safety Versus Resilience
The SEF specifies practices for managing safety and resilience dangers. The attitude the group adopts—safety, resilience, or a mix of the 2—influences the dangers an acquisition group considers throughout an evaluation and the set of controls which might be accessible for threat mitigation. Due to the associated nature of safety and resilience, the SEF (and the rest of this weblog submit) makes use of the time period safety/resilience all through.
SEF Construction
As illustrated in Determine 3, the SEF has a hierarchy of domains, targets, and practices:
- Domains occupy the highest degree of the SEF hierarchy. A website captures a novel administration or technical perspective of managing safety/resilience dangers throughout the programs lifecycle. Every area is supported by two or extra targets, which kind the subsequent degree of the SEF hierarchy.
- Targets outline the capabilities {that a} program leverages to construct safety/resilience right into a software-reliant system. Associated targets belong to the identical SEF area.
- Practices inhabit the ultimate and most detailed degree within the hierarchy. Practices describe actions that help the achievement of SEF targets. The SEF phrases practices as questions. Associated practices belong to the identical SEF purpose.
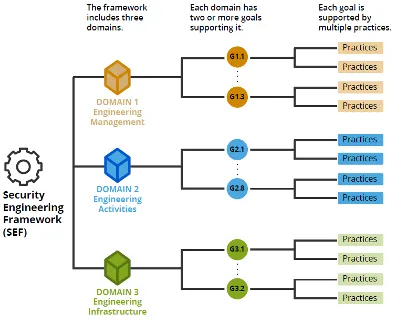
Determine 3: SEF Group and Construction
The SEF includes 3 domains, 13 targets, and 119 practices. The subsequent part describes the SEF’s domains and targets.
Area 1: Engineering Administration
This area supplies a basis for fulfillment by guaranteeing that safety/resilience actions are deliberate and managed. The target of Area 1 is to handle safety/resilience dangers successfully within the system being acquired and developed.
Program and engineering managers mix their technical experience with their enterprise and mission information to supply technical administration and organizational management for engineering initiatives. Managers are tasked with planning, organizing, and directing an acquisition program’s engineering and growth actions. Engineering administration is a specialised sort of administration that’s wanted to guide engineering or technical personnel and initiatives efficiently. Area 1 includes the next three targets:
- Aim 1.1: Engineering Exercise Administration. Safety/resilience engineering actions throughout the lifecycle are deliberate and managed.
- Aim 1.2: Engineering Threat Administration. Safety/resilience dangers that may have an effect on the system are assessed and managed throughout system design and growth.
- Aim 1.3: Unbiased Evaluation. An impartial evaluation of this system or system is carried out.
Area 2: Engineering Actions
This area addresses the day-to-day practices which might be important for constructing safety/resilience right into a software-reliant system. The target of Area 2 is to combine safety/resilience into this system’s present engineering practices. All programs lifecycles handle a typical set of engineering actions, starting with necessities specification and persevering with via system O&S. Area 2 expands the main target of a program’s programs lifecycle mannequin to incorporate safety/resilience. Area 2 includes the next eight targets:
- Aim 2.1: Necessities. Safety/resilience necessities for the system and its software program parts are specified, analyzed, and managed.
- Aim 2.2: Structure. Safety/resilience dangers ensuing from the system and software program architectures are assessed and mitigated.
- Aim 2.3: Third-Social gathering Elements. Safety/resilience dangers that may have an effect on third-party parts are recognized and mitigated.
- Aim 2.4: Implementation. Safety/resilience controls are applied, and weaknesses and vulnerabilities in software program code are assessed and managed.
- Aim 2.5: Check and Analysis. Safety/resilience dangers that may have an effect on the built-in system are recognized and remediated throughout take a look at and analysis.
- Aim 2.6: Authorization to Function. The operation of the system is permitted, and the residual threat to operations is explicitly accepted.
- Aim 2.7: Deployment. Safety/resilience is addressed in transition and deployment actions.
- Aim 2.8: Operations and Sustainment. Safety/resilience dangers and points are recognized and resolved because the system is used and supported within the operational atmosphere.
Area 3: Engineering Infrastructure
This area manages safety/resilience dangers within the engineering, growth, take a look at, and coaching environments. The goals of Area 3 are to make use of software program, instruments, and applied sciences that help this system’s engineering and growth actions and to handle safety/resilience dangers within the engineering infrastructure. Engineers and builders use a wide range of software program, instruments, and applied sciences to help their design and growth actions. Safety/resilience engineering software program, instruments, and applied sciences should be procured, put in, and built-in with this system’s present engineering infrastructure.
The engineering infrastructure is the a part of the IT infrastructure that helps engineering and growth actions carried out by personnel from the acquisition program, contractors, and suppliers. Because of this, the engineering infrastructure might be an assault vector into the software-reliant system that’s being acquired and developed. IT help groups want to make sure that they’re making use of safety/resilience practices when managing the engineering infrastructure to make sure that threat is being managed appropriately. Area 3 includes the next two targets:
- Aim 3.1: Engineering Software program, Instruments, and Applied sciences. Safety/resilience engineering software program, instruments, and applied sciences are built-in with the engineering infrastructure.
- Aim 3.2: Infrastructure Operations and Sustainment. Safety/resilience dangers within the engineering infrastructure are recognized and mitigated.
SEF Practices and Steerage
SEF domains present the organizing construction for the framework’s technical content material, which is the gathering of targets and practices. The SEF’s in-depth steerage for all targets and practices describes the potential represented by every purpose, together with its function, related context, and supporting practices. SEF steerage additionally defines the important thing ideas and background info wanted to know the intent of every apply.
Safety Engineering Framework (SEF): Managing Safety and Resilience Dangers Throughout the Programs Lifecycle accommodates in-depth steerage for all targets and practices.
Accomplice with the SEI to Handle Safety and Resilience Dangers
The SEF paperwork main engineering practices for managing safety/resilience dangers throughout the programs lifecycle. The SEI supplies open entry to SEF steerage, strategies, and supplies. Future work associated to the SEF will focus totally on transitioning SEF ideas and practices to the group. The SEI plans to work with DoD applications to pilot the SEF and incorporate classes realized into future model of the framework.
Lastly, the SEF growth workforce continues to hunt suggestions on the framework, together with how it’s getting used and utilized. This info will assist affect the long run path of the SEF in addition to the SEI’s work on documenting main practices for software program safety.

