In Cloudera deployments on public cloud, one of many key configuration components is the DNS. Get it flawed and your deployment could develop into wholly unusable with customers unable to entry and use the Cloudera information providers. If the DNS is ready up much less excellent than it might be, connectivity and efficiency points could come up. On this weblog, we’ll take you thru our tried and examined finest practices for organising your DNS to be used with Cloudera on Azure.
To get began and offer you a really feel for the dependencies for the DNS, in an Azure deployment for Cloudera, these are the Azure managed providers getting used:
- AKS cluster: information warehouse, information engineering, machine studying, and Knowledge movement
- MySQL database: information engineering
- Storage account: all providers
- Azure database for PostgreSQL DB: information lake and information hub clusters
- Key vault: all providers
Typical buyer governance restrictions and the impression
Most Azure customers use non-public networks with a firewall as egress management. Most customers have restrictions on firewalls for wildcard guidelines. Cloudera sources are created on the fly, which implies wildcard guidelines could also be declined by the safety crew.
Most Azure customers use hub-spoke community topology. DNS servers are often deployed within the hub digital community or an on-prem information middle as an alternative of within the Cloudera VNET. Meaning if DNS just isn’t configured appropriately, the deployment will fail.
Most Cloudera clients deploying on Azure permit using service endpoints; there’s a smaller set of organizations that don’t permit using service endpoints. Service endpoint is a less complicated implementation to permit sources on a personal community to entry managed providers on Azure Cloud. If service endpoints are usually not allowed, firewall and personal endpoints would be the different two choices. Most cloud customers don’t like opening firewall guidelines as a result of that may introduce the danger of exposing non-public information on the web. That leaves non-public endpoints the one possibility, which may also introduce extra DNS configuration for the non-public endpoints.
Connectivity from non-public community to Azure managed providers
Firewall to Web
Route from firewall to Azure managed service endpoint on the web instantly.
Service endpoint
Azure gives service endpoints for sources on non-public networks to entry the managed providers on the web with out going via the firewall. That may be configured at a subnet stage. Since Cloudera sources are deployed in several subnets, this configuration have to be enabled on all subnets.
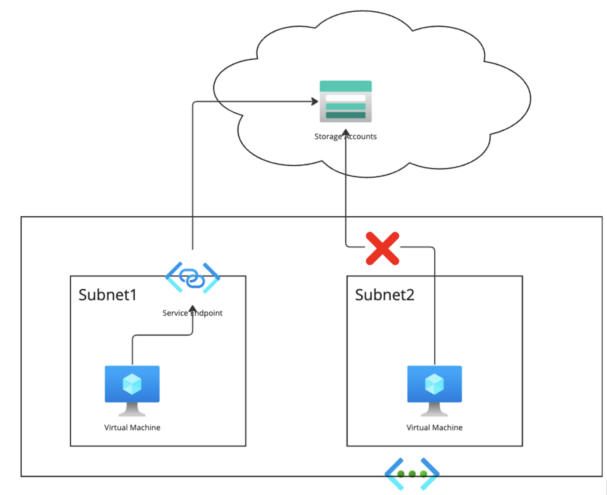
The DNS information of the managed providers utilizing service endpoints can be on the web and managed by Microsoft. The IP deal with of this service can be a public IP, and routable from the subnet. Please seek advice from the Microsoft documentation for element.
Not all managed providers help providers endpoint. In a Cloudera deployment state of affairs, solely storage accounts, PostgreSQL DB, and Key Vault help service endpoints.
Happily, most customers permit service endpoints. If a buyer doesn’t permit service endpoints, they should go along with a personal endpoint, which is analogous to what must be configured within the following content material.
Non-public Endpoint
There’s a community interface with a personal IP deal with created with a personal endpoint, and there’s a non-public hyperlink service related to a particular community interface, in order that different sources within the non-public community can entry this service via the non-public community IP deal with.
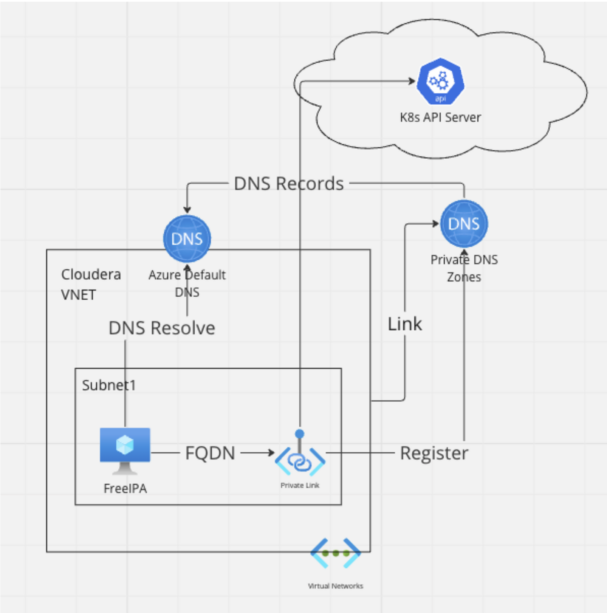
The important thing right here is for the non-public sources to discover a DNS resolve for that personal IP deal with. There are two choices to retailer the DNS report:
- Azure managed public DNS zones will at all times be there, however they retailer several types of IP addresses for the non-public endpoint. For instance:
- Storage account non-public endpoint—the general public DNS zone shops the general public IP deal with of that service.
- AKS API server non-public endpoint—the general public DNS zone shops the non-public IP of that service.
- Azure Non-public DNS zone: The DNS information can be synchronized to the Azure Default DNS of LINKED VNET.
Non-public endpoint is eligible to all Azure managed providers which might be utilized in Cloudera deployments.
As a consequence, for storage accounts, customers both use service endpoints or non-public endpoints. As a result of the general public DNS zone will at all times return a public IP, the non-public DNS zone turns into a compulsory configuration.
For AKS, these two DNS options are each appropriate. The challenges of personal DNS zones can be mentioned subsequent.
Challenges of personal DNS zone on Azure non-public community
Essential Assumptions
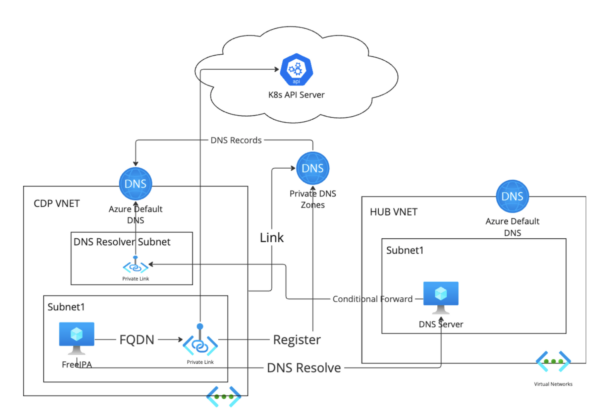
As talked about above for the standard state of affairs, most Azure customers are utilizing a hub-and-spoke community structure, and deploy customized non-public DNS on hub VNET.
The DNS information can be synchronized to Azure default DNS of linked VNET.
Easy Structure Use Circumstances
One VNET state of affairs with non-public DNS zone:
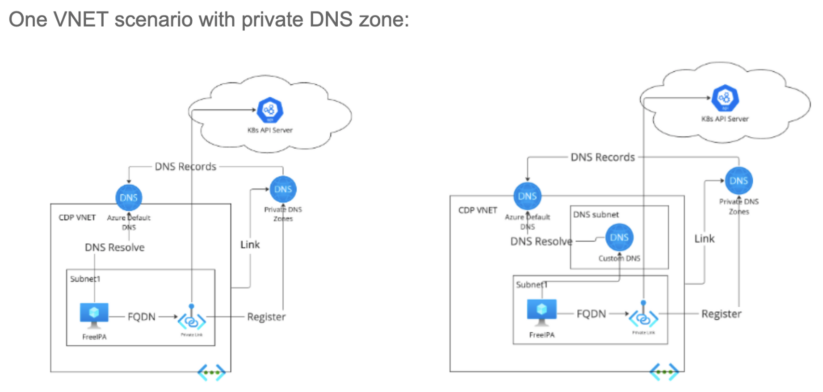
When a personal endpoint is created, Cloudera on Azure will register the non-public endpoint to the non-public DNS zone. The DNS report can be synchronized to Azure Default DNS of linked VNET.
If customers use customized non-public DNS, they will configure conditional ahead to Azure Default DNS for the area suffix of the FQDN.
Hub-and-spoke VNET with Azure default DNS:
 With hub-spoke VNET and Azure default DNS, that’s nonetheless acceptable. The one drawback is that the sources on the un-linked VNET won’t be able to entry the AKS. However since AKS is utilized by Cloudera, that doesn’t pose any main points.
With hub-spoke VNET and Azure default DNS, that’s nonetheless acceptable. The one drawback is that the sources on the un-linked VNET won’t be able to entry the AKS. However since AKS is utilized by Cloudera, that doesn’t pose any main points.
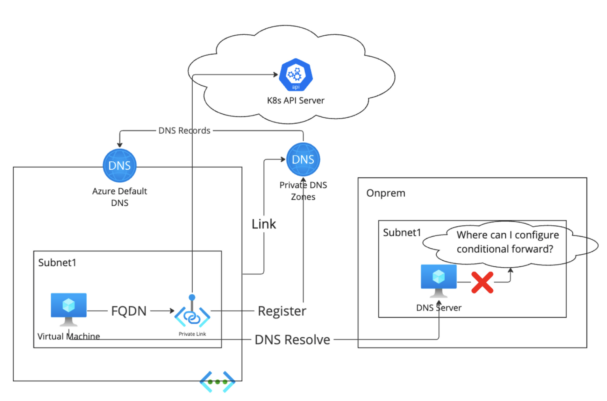
The Problem Half
The most well-liked community structure amongst Azure customers is hub-spoke community with customized non-public DNS servers deployed both on hub-VNET or on-premises community.
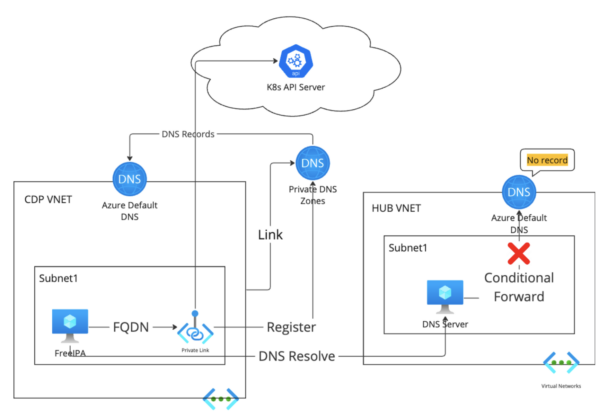
Since DNS information are usually not synchronized to the Azure Default DNS of the hub VNET, the customized non-public DNS server can’t discover the DNS report for the non-public endpoint. And since the Cloudera VNET is utilizing the customized non-public DNS server on hub VNET, the Cloudera sources on Cloudera VNET will go to a customized non-public DNS server for DNS decision of the FQDN of the non-public endpoint. The provisioning will fail.
With the DNS server deployed within the on-prem community, there isn’t Azure default DNS related to the on-prem community, so the DNS server couldn’t discover the DNS report of the FQDN of the non-public endpoint.
Configuration finest practices
Towards the background
Possibility 1: Disable Non-public DNS Zone
Use Azure managed public DNS zone as an alternative of a personal DNS zone.
- For information warehouse: create information warehouses via the Cloudera command line interface with the parameter “privateDNSZoneAKS”: set to”None.”
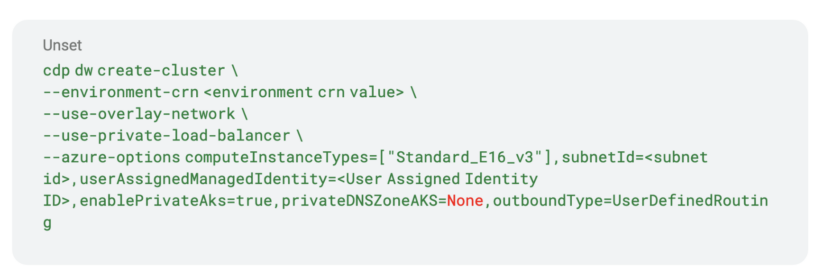
- For Liftie-based information providers: the entitlement “LIFTIE_AKS_DISABLE_PRIVATE_DNS_ZONE” have to be set. Clients can request this entitlement to be set both via a JIRA ticket or have their Cloudera resolution engineer to make the request on their behalf.
The only disadvantage of this feature is that it doesn’t apply to information engineering, since that information service will create and use a MySQL non-public DNS zone on the fly. There’s at current no choice to disable non-public DNS zones for information engineering.
Possibility 2: Pre-create Non-public DNS Zones
Pre-create non-public DNS zones and hyperlink each Cloudera and hub VNETs to them.
The benefit of this strategy is that each information warehouse and Liftie-based information providers help pre-created non-public DNS zones. There are nevertheless additionally just a few drawbacks:
- For Liftie, the non-public DNS zone must be configured when registering the atmosphere. As soon as previous the atmosphere registration stage, it can’t be configured.
- DE will want a personal DNS zone for MySQL and it doesn’t help pre-configured non-public DNS zones.
- On-premises networks can’t be linked to a personal DNS zone. If the DNS server is on an on-prem community, there aren’t any workable options.
Possibility 3: Create DNS Server as a Forwarder.
Create a few DNS servers (for HA consideration) with load balancer in Cloudera VNET, and configure conditional ahead to Azure Default DNS of the Cloudera VNET. Configure conditional ahead from the corporate customized non-public DNS server to the DNS server within the Cloudera subnet.
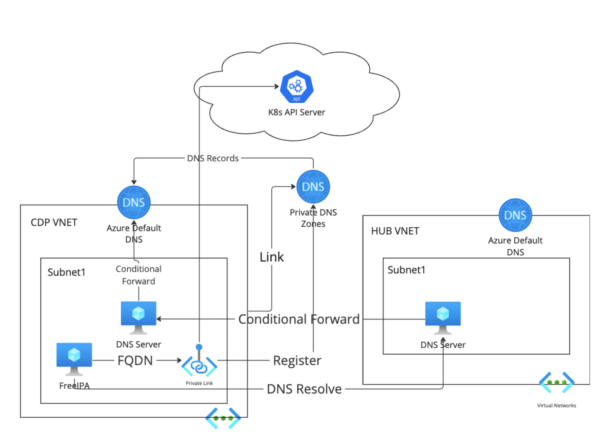
The disadvantage of this feature is that extra DNS servers are required, which ends up in extra administration overhead for the DNS crew.
Possibility 4: Azure-Managed DNS Resolve
Create a devoted /28 subnet in Cloudera VNET for Azure non-public DNS resolver inbound endpoint. Configure conditional ahead from customized non-public DNS to the Azure non-public DNS resolver inbound endpoint.
Abstract
Bringing all issues collectively, contemplate these finest practices for organising your DNS with Cloudera on Azure:
- For the storage account, key vault, postgres DB
- Use service endpoints as the primary selection.
- If service endpoint just isn’t allowed, pre-create non-public DNS zones and hyperlink to the VNET the place the DNS server is deployed. Configure conditional forwards from customized non-public DNS to Azure default DNS.
- If the customized non-public DNS is deployed within the on-premises community, use Azure DNS resolver or one other DNS server as DNS forwarder on the Cloudera VNET. Conditional ahead the DNS lookup from the non-public DNS to the resolver endpoint.
- For the info warehouse, DataFlow, or machine studying information providers
- Disable the non-public DNS zone and use the general public DNS zone as an alternative.
- For the info engineering information service
- Configure the Azure DNS resolver or one other DNS server as a DNS forwarder on the Cloudera VNET. Conditional ahead the DNS lookup from the non-public DNS to the resolver endpoint. Please seek advice from Microsoft documentation for the small print of organising an Azure DNS Non-public Resolver.
For extra background studying on community and DNS specifics for Azure, take a look at our documentation for the assorted information providers: DataFlow, Knowledge Engineering, Knowledge Warehouse, and Machine Studying. We’re additionally comfortable to debate your particular wants; in that case please attain out to your Cloudera account supervisor or get in contact.


