
A vulnerability within the DanaBot malware operation launched in June 2022 replace led to the identification, indictment, and dismantling of their operations in a current legislation enforcement motion.
DanaBot is a malware-as-a-service (MaaS) platform energetic from 2018 via 2025, used for banking fraud, credential theft, distant entry, and distributed denial of service (DDoS) assaults.
Zscaler’s ThreatLabz researchers who found the vulnerability, dubbed ‘DanaBleed,’ clarify {that a} reminiscence leak allowed them to realize a deep peak into the malware’s inner operations and the folks behind it.
Leveraging the flaw to gather precious intelligence on the cybercriminals enabled a world legislation enforcement motion named ‘Operation Endgame‘ to take DanaBot infrastructure offline and indict 16 members of the menace group.
DanaBleed
The DanaBleed flaw was launched in June 2022 with DataBot model 2380, which added a brand new command and management (C2) protocol.
A weak point within the new protocol’s logic was within the mechanism that generated the C2 server’s responses to shoppers, which was supposed to incorporate randomly generated padding bytes however did not initialize newly allotted reminiscence for these.
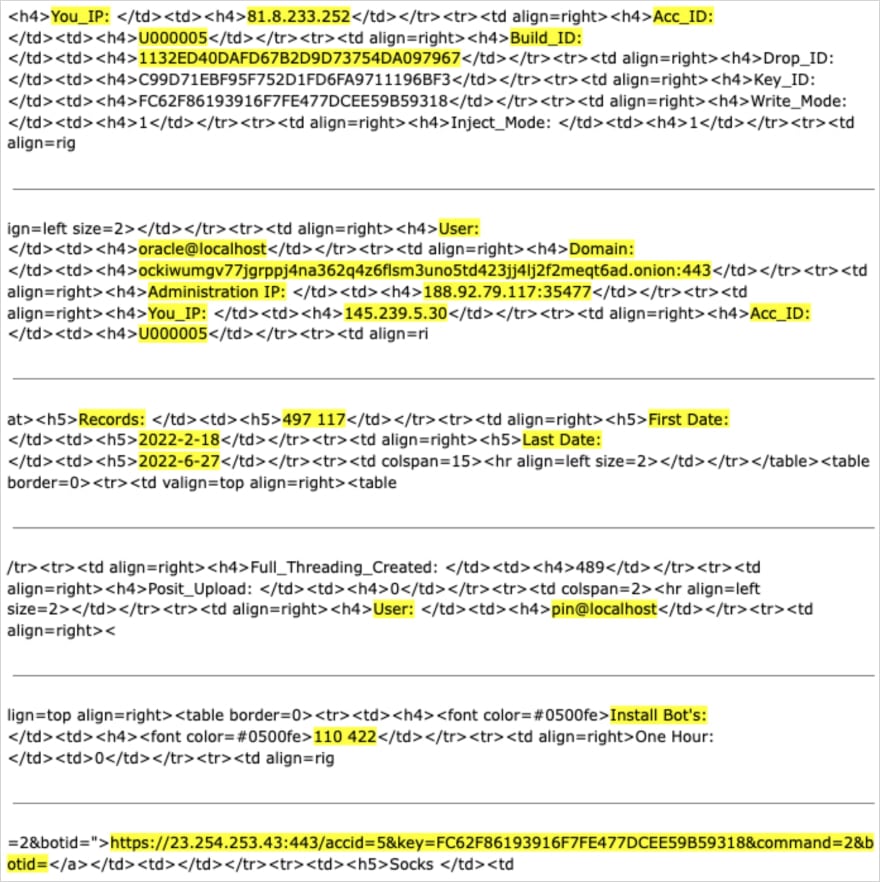
Zscaler researchers collected and analyzed a lot of C2 responses that, because of the reminiscence leak bug, contained leftover information fragments from the server’s reminiscence.
This publicity is analogous to the HeartBleed drawback found in 2014, impacting the ever-present OpenSSL software program.
Because of DanaBleed, a broad array of personal information was uncovered to the researchers over time, together with:
- Risk actor particulars (usernames, IP addresses)
- Backend infrastructure (C2 server IPs/domains)
- Sufferer information (IP addresses, credentials, exfiltrated data)
- Malware changelogs
- Personal cryptographic keys
- SQL queries and debug logs
- HTML and internet interface snippets from the C2 dashboard
For over three years, DanaBot operated in a compromised mode with out its builders or shoppers ever realizing they have been being uncovered to safety researchers.
This allowed focused legislation enforcement motion when sufficient information had been collected.
Supply: Zscaler
Though DanaBot’s core staff in Russia was merely indicted and never arrested, the seizure of important C2 servers, 650 domains, and almost $4,000,000 in cryptocurrency has successfully neutralized the menace for now.
It’s not unlikely that the menace actors try to return to cybercrime operations sooner or later, however diminished belief from the hackers’ neighborhood shall be a major impediment for them.
Patching used to imply complicated scripts, lengthy hours, and countless fireplace drills. Not anymore.
On this new information, Tines breaks down how fashionable IT orgs are leveling up with automation. Patch sooner, scale back overhead, and deal with strategic work — no complicated scripts required.


