
A vital Citrix NetScaler vulnerability, tracked as CVE-2025-5777 and dubbed “CitrixBleed 2,” was actively exploited practically two weeks earlier than proof-of-concept (PoC) exploits have been made public, regardless of Citrix stating that there was no proof of assaults.
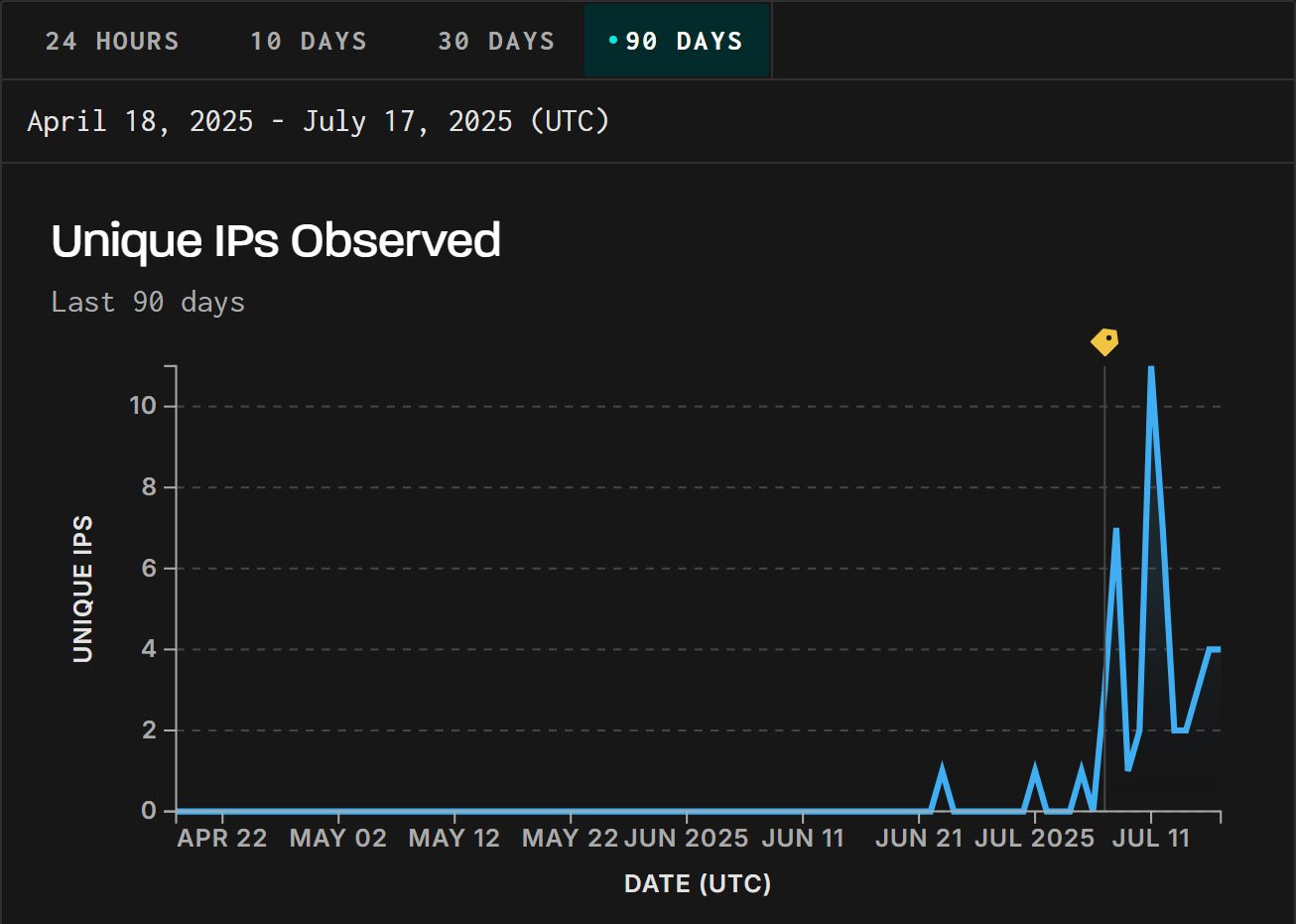
GreyNoise has confirmed its honeypots detected focused exploitation from IP addresses situated in China on June 23, 2025.
“GreyNoise has noticed energetic exploitation makes an attempt towards CVE-2025-5777 (CitrixBleed 2), a reminiscence overread vulnerability in Citrix NetScaler. Exploitation started on June 23 — practically two weeks earlier than a public proof-of-concept (PoC) was launched on July 4,” explains GreyNoise.
“We created a tag on July 7 to trace this exercise. As a result of GreyNoise retroactively associates pre-tag site visitors with new tags, prior exploitation makes an attempt at the moment are seen within the GreyNoise Visualizer.”
Supply: BleepingComputer
GreyNoise confirmed to the U.S. Cybersecurity and Infrastructure Safety Company (CISA) on July 9 that the flaw was actively exploited, inflicting the cyber company so as to add it to its Recognized Exploited Vulnerabilities (KEV) catalog and giving federal businesses someday to patch the flaw.
GreyNoise shared the exploit used within the June assaults with BleepingComputer and we are able to verify that it’s the one for Citrix Bleed 2, demonstrating that risk actors have been actively exploiting it earlier than the PoCs have been launched.
Regardless of these early indicators and repeated warnings from safety researcher Kevin Beaumont, Citrix had nonetheless not acknowledged energetic exploitation in its safety advisory for CVE-2025-5777. It solely quietly up to date its June 26 weblog submit on July 11, after it appeared within the KEV database the day earlier than.
Citrix lastly launched one other weblog submit on July 15 on the way to consider NetScaler logs for indicators of compromise.
Nevertheless, even with this, the corporate has been underneath fireplace for not being clear and sharing IOCs that researchers have advised BleepingComputer have been beforehand shared with the corporate.
Citrix has additionally not responded to BleepingComputer’s questions on why the unique CVE-2025-5777 advisory nonetheless doesn’t acknowledge exploitation.
The Citrix Bleed 2 vulnerability
Citrix Bleed 2 is a vital 9.3 severity vulnerability attributable to inadequate enter validation, which permits attackers to ship malformed POST requests to NetScaler home equipment throughout login makes an attempt.
That is exploited by omitting the equal signal within the “login=” parameter, inflicting the machine to leak 127 bytes of reminiscence. Researchers from Horizon3 and WatchTowr demonstrated that repeated requests can be utilized to show delicate information akin to legitimate session tokens.
These tokens can then be used to hijack Citrix classes and acquire unauthorized entry to inner assets.
Safety researcher Kevin Beaumont has beforehand acknowledged that repeated POST requests to /doAuthentication.do in NetScaler logs is an efficient indication that somebody is making an attempt to use the flaw, particularly when the request features a Content material-Size: 5 header.
Different indications embody log entries displaying person logoffs the place the username consists of surprising characters, akin to “#”, or reminiscence contents printed into incorrect fields.
Beaumont additionally warned that Citrix’s steering fails to completely clear compromised classes.
Whereas Citrix recommends terminating ICA and PCoIP classes utilizing kill icaconnection -all and kill pcoipConnection -all, Beaumont advises additionally to terminate different session varieties which will have hijacked classes:
kill pcoipConnection -all
kill icaconnection -all
kill rdpConnection -all
kill sshConnection -all
kill telnetConnection -all
kill connConnection -all
kill aaa session -allAdmins also needs to overview all classes earlier than terminating them to examine for suspicious logins, akin to sudden IP deal with modifications or unauthorized customers.
Citrix’s July 15 weblog submit shares additional steering on figuring out indicators of exploitation, akin to log entries displaying the next messages:
- “Authentication is rejected for”
- “AAA Message”
- Non-ASCII byte values (0x80–0xFF)
Session logs will also be manually inspected for uncommon IP deal with modifications related to the identical session. For instance, in VPN logs, a mismatch between the client_ip and the supply IP deal with could point out {that a} session was hijacked.
In a current submit, Beaumont states that he has been monitoring the exploitation since June, with over 120 firms already compromised by the flaw.
“Entry began June 20 2025, with entry ramping up from June 21 to this as of writing,” warns Beaumont.
“I believe the exercise I see could also be one risk actor group — there could also be extra. They’re cautious in deciding on victims, profiling Netscaler earlier than attacking to ensure it’s a actual field — e.g. they did not fall into any of my honeypots.”
The researcher additionally warns that Citrix’s personal Internet Utility Firewall at the moment doesn’t detect exploitation of CVE-2025-5777. Nevertheless, Imperva stories that their product has detected over 11.5 million makes an attempt to use this flaw, with 40% concentrating on the monetary sector.
Citrix has launched patches for NetScaler ADC and Gateway variations and is strongly urging instant upgrades.
There are not any mitigations past patching, and clients working EOL variations (12.1 and 13.0) ought to improve to supported builds.
CISOs know that getting board buy-in begins with a transparent, strategic view of how cloud safety drives enterprise worth.
This free, editable board report deck helps safety leaders current danger, affect, and priorities in clear enterprise phrases. Flip safety updates into significant conversations and quicker decision-making within the boardroom.


