We have all been there. You attempt to log into your checking account together with your username and password solely to be met with a generic “incorrect password” error. You double-check your password supervisor, strive just a few variations, however after too many failed makes an attempt, the system locks you out. Now you are funneled right into a tedious re-authentication course of involving safety questions you barely bear in mind and a password reset kind that smugly informs you, “New password cannot be the identical because the previous one.” You proceed to throw your machine in frustration.
What’s a Passkey?
A passkey is a safe, easy-to-use substitute for passwords. It makes use of your machine’s built-in safety (like Face ID, fingerprint, or a PIN) to log you into an internet site or service, with out requiring you to recollect or sort something.
The passkey is then saved on a safe factor of your telephone or laptop, which implies the web site or service you are accessing will not must retailer any passwords on their servers – decreasing the chance of breaches or hacks.
In sensible phrases, you can say passkeys merge the idea of a password and 2FA (two-factor authentication) into one clean motion, however far more safe and method much less annoying.
As an non-compulsory and really helpful step, you’ll be able to retailer your passkeys inside a safe password supervisor reminiscent of Proton Cross, 1Password, Dashlane, or Bitwarden. This lets you sync and entry your passkeys throughout a number of gadgets.
Making a Passkey
Making a passkey is simple, and the method is analogous throughout most platforms. For example, here is how we arrange a passkey for Amazon.com and used a password supervisor to retailer it…
First, I log into my Amazon account and navigate to the Login & Safety part to entry the passkey choice.
Subsequent, I click on on “Add a passkey,” which creates a passkey particularly for Amazon. As proven within the screenshot, I had beforehand created a passkey that is saved in my iCloud Keychain. You’ll be able to create a number of passkeys for a similar web site and retailer them somewhere else.
As a result of I exploit Proton Cross and I’ve their browser extension put in, including a passkey routinely opens Proton Cross to generate and retailer it. If I did not have Proton Cross put in, my net browser (Chrome, Firefox, and many others.) would have saved the passkey as a substitute.
Proton Cross will now save this particular passkey for Amazon, synced to my username. Since that is for Amazon, it additionally works for Amazon Net Providers (AWS) accounts.
Why are Passkeys Wanted?
In accordance with NordPass’s analysis, the hottest password stays “123456” as of 2023 and 2024. The second hottest? “123456789.” Different frequent passwords are often strings of sequential numbers or variations on “qwerty.” After six years of the identical research, NordPass concludes that most individuals’s password habits have not meaningfully modified.
| Characteristic | Password + 2FA | Passkey |
|---|---|---|
| Steps | A number of | Single |
| Consumer must… | Kind & wait | Simply verify |
| Safety | Good | Higher (phishing-resistant) |
| Comfort | Medium | Excessive |
Passkeys are safer as a result of they eradicate password-based vulnerabilities, changing passwords with cryptographic keys that shield customers from phishing assaults, credential theft, and information breaches. Passkeys are protected by a single biometric issue, like your fingerprint or face, and no passwords are despatched over the web or saved on exterior servers.
The place Can I Use Passkeys?
Whereas not each service has carried out passkey authentication, hottest websites have. A number of the main ones that help it embrace Amazon, Google, Apple, Github, Adobe, Uber, Microsoft, Nintendo, PlayStation Community, eBay, and Dropbox, in addition to many social networks.
Monetary establishments (banks) lag behind massive tech giants in adopting passkeys, nevertheless firms like PayPal, Revolut and Robinhood already help it. Dashlane provides a useful, community-driven listing of internet sites which have carried out passkeys login performance.
You’ll be able to already create passkeys utilizing Google, Microsoft, or Apple gadgets. Many password managers – reminiscent of Proton Cross, Dashlane, 1Password, Bitwarden, and LastPass – additionally help passkey creation. As talked about earlier, utilizing a password supervisor permits passkeys to sync throughout gadgets.
It is also necessary to do not forget that passkeys are distinctive to every web site. The passkey you utilize to signal into your Google account is just not the identical because the one used for Amazon. That stated, a useful professional tip is to create a passkey on your Google account after which use Google’s authentication to check in to different providers (if the choice exists). That method you’ll be able to simply use your one Google passkey whereas having the ability to entry a number of web sites.
How Passkeys Work (Technical Rationalization)
Passkeys (technically often known as Net Authentication or WebAuthn) are a know-how that permits credentials to be authenticated with out being saved on servers. They’re a part of the FIDO2 venture, which goals to completely exchange passwords as a way of authentication.
The core idea depends on public key infrastructure (PKI). As an alternative of storing a username and password, passkeys are generated on an authenticator managed by the person.
This authenticator might be your smartphone (Face ID, fingerprint), your working system (e.g., Home windows Hi there), your browser, or a bodily safety key reminiscent of a YubiKey or Google’s Titan Key.
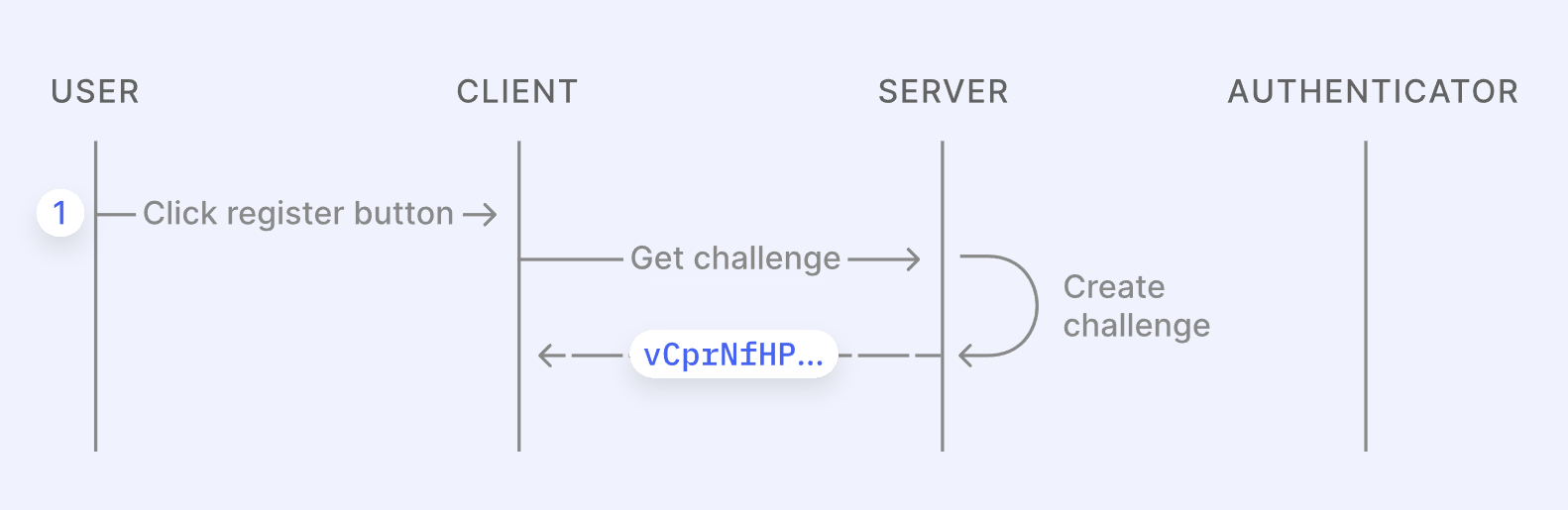
Making a passkey is a 3-step course of:
- The person clicks a button on a consumer (like Google) to create a passkey. This sends a request to the server, which responds with a randomly generated problem string.
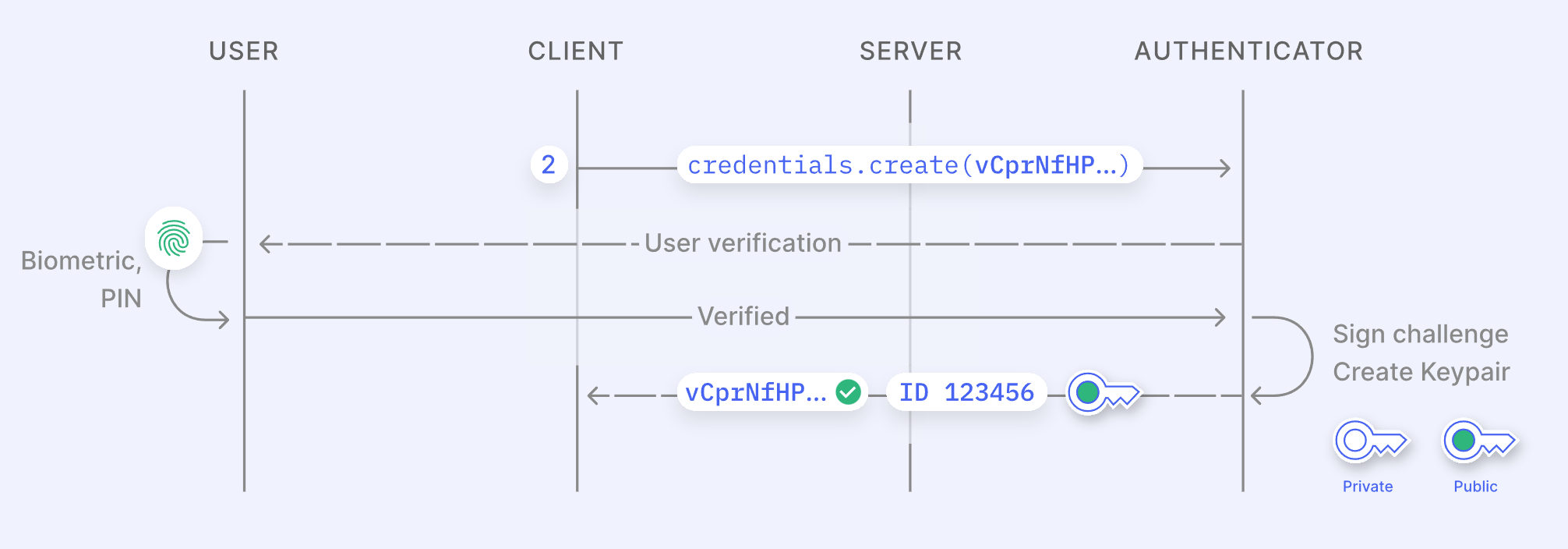
- The consumer calls the WebAuthn API together with the server’s problem to create a non-public/public key pair. This key pair is generated and saved securely on the machine in a safe factor reminiscent of a Trusted Platform Module (TPM) chip or Apple’s iCloud Keychain. Relying on the consumer, the person is prompted for a PIN or biometric authentication (e.g., Face ID, Home windows Hi there, or fingerprint).
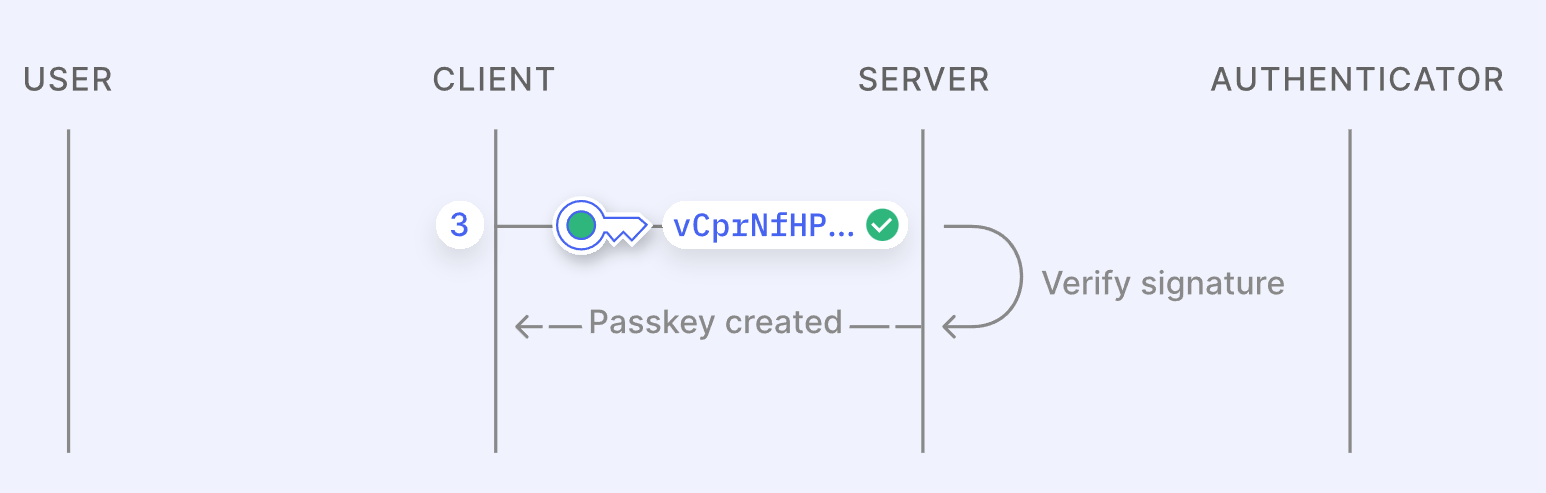
- The consumer sends the general public key, credential ID, and the signed problem (utilizing the non-public key) again to the server. For future logins, the person authenticates through their machine, which indicators a brand new problem and sends it to the server. The server validates this by matching the credential ID and public key to the signed problem. If it checks out, the person is efficiently logged in.
Regularly Requested Questions
What occurs if I lose my machine?
Passkeys require biometric authentication in your telephone. Even when your telephone is stolen, the passkeys cannot be accessed with out your biometric information.
Can I share a passkey with another person?
The aim of passkeys is to offer private, identity-bound authentication – not shared credentials. However technically, sure, there are methods to share passkeys.
For instance, Apple permits passkeys to be shared through AirDrop beneath sure circumstances. It’s also possible to share passkeys by logging into the identical password supervisor.
Can passkeys forestall phishing makes an attempt?
Completely. Phishing sometimes goals to steal usernames, passwords, or delicate information. Passkeys do not transmit credentials, making them ineffective to an attacker even when intercepted.
What if somebody hacks the server or database?
At most, an attacker would possibly achieve entry to the general public keys saved within the database. Since these cannot be used to reverse-engineer your non-public key, your account stays safe. If wanted, you’ll be able to merely revoke the previous passkey and generate a brand new one.
What about simply utilizing a password supervisor?
Whereas password managers are step up from remembering passwords, they nonetheless depend on storing credentials on a server. Even open-source choices like KeePass require a database of passwords. In distinction, passkeys present a safer and simplified answer by eradicating the necessity to handle or retailer a number of credentials.
Are there any situations the place passkeys aren’t wanted?
Sure. Whereas passkeys supply a safer and user-friendly various to conventional passwords, they are not mandatory – and even perfect – in each situation. Listed here are just a few examples:
- Low-security accounts
If an account would not retailer delicate data (e.g., a throwaway discussion board account or a neighborhood information website), a powerful password should still be “ok.” Shared accounts
Passkeys are tied to you and your machine. So for accounts shared amongst a number of folks (like a shared Netflix account or enterprise login), conventional passwords nonetheless work extra flexibly – for now.Enterprise or legacy methods
Older company methods, VPNs, or inner instruments could not help passkeys in any respect – some industries transfer slowly in the case of adopting new authentication tech.Non-person entities (NPEs)
Builders utilizing automated methods or scripts, they might must authenticate to a server to carry out duties like scanning or information processing. In such circumstances, passkeys aren’t sensible. This might additionally lengthen to software program needing to make use of authentication for safe API calls.
Moreover, there are environments the place passkey adoption simply would not match but. If you happen to’re on a tool that lacks cloud backup or passkey syncing, reminiscent of an older smartphone or a public laptop, it may be tough or unattainable to make use of passkeys successfully.
So whereas passkeys are the way forward for authentication, there are nonetheless legitimate causes to stay with passwords in sure contexts – for now.






