
The RansomHub ransomware gang is behind the latest cyberattack on oil and gasoline providers large Halliburton, which disrupted the corporate’s IT methods and enterprise operations.
The assault brought about widespread disruption, and BleepingComputer was informed that prospects could not generate invoices or buy orders as a result of the required methods had been down.
Halliburton disclosed the assault final Friday in an SEC submitting, stating they suffered a cyberattack on August 21, 2024, by an unauthorized social gathering.
“On August 21, 2024, Halliburton Firm (the “Firm”) grew to become conscious that an unauthorized third social gathering gained entry to sure of its methods,” learn Halliburton’s SEC submitting.
“When the Firm realized of the difficulty, the Firm activated its cybersecurity response plan and launched an investigation internally with the help of exterior advisors to evaluate and remediate the unauthorized exercise.”
The corporate offers a quite a few providers to grease and gasoline firms, together with properly development, drilling, hydraulic fracturing (fracking), and IT software program and providers. As a result of firm’s big selection of providers, there may be an excessive amount of connectivity between them and their prospects.
Nonetheless, the corporate has not shared many particulars in regards to the assault, with a buyer within the oil and gasoline business telling BleepingComputer that they’ve been left at midnight about figuring out if the assault impacted them and the way to defend themselves.
This has brought about different prospects to disconnect from Halliburton as a result of lack of knowledge being shared.
BleepingComputer has additionally been informed that some firms are working with ONG-ISAC—an company that acts as a central level of coordination and communication for bodily and cybersecurity threats towards the oil and gasoline business—to obtain technical details about the assault to find out in the event that they had been breached as properly.
RansomHub ransomware behind the assault
For days, there have been rumors that Halliburton suffered a RansomHub ransomware assault, with customers claiming this on Reddit and on the job layoff dialogue website, TheLayoff, the place a partial RansomHub ransom word was printed.
When BleepingComputer contacted Halliburton about these claims, Halliburton stated they weren’t making any additional feedback.
“We’re not commenting past what was included in our submitting. Any subsequent communications shall be within the type of an 8-Okay,” Halliburton informed BleepingComputer.
Nonetheless, in an August 26 e mail despatched to suppliers and shared with BleepingComputer, Halliburton offered further info stating that the corporate took methods offline to guard them and is working with Mandiant to research the incident.
“We’re reaching out to replace you a few cybersecurity situation affecting Halliburton,” reads the letter seen by BleepingComputer.
“As quickly as we realized of the difficulty, we activated our cybersecurity response plan and took steps to deal with it, together with (1) proactively taking sure methods offline to assist defend them, (2) partaking the help of main exterior advisors, together with Mandiant, and (3) notifying legislation enforcement.”
In addition they acknowledged that their e mail methods proceed to function as they’re hosted on Microsoft Azure infrastructure. A workaround can also be out there for transacting and issuing buy orders.
This e mail features a record of IOCs containing file names and IP addresses related to the assault that prospects can use to detect comparable exercise on their community.
Certainly one of these IOCs is for a Home windows executable named upkeep.exe, which BleepingComputer has confirmed to be a RansomHub ransomware encryptor.
After analyzing the pattern, it seems to be a more recent model than beforehand analyzed, because it comprises a brand new “-cmd string” command-line argument, which is able to execute a command on the gadget earlier than encrypting recordsdata.
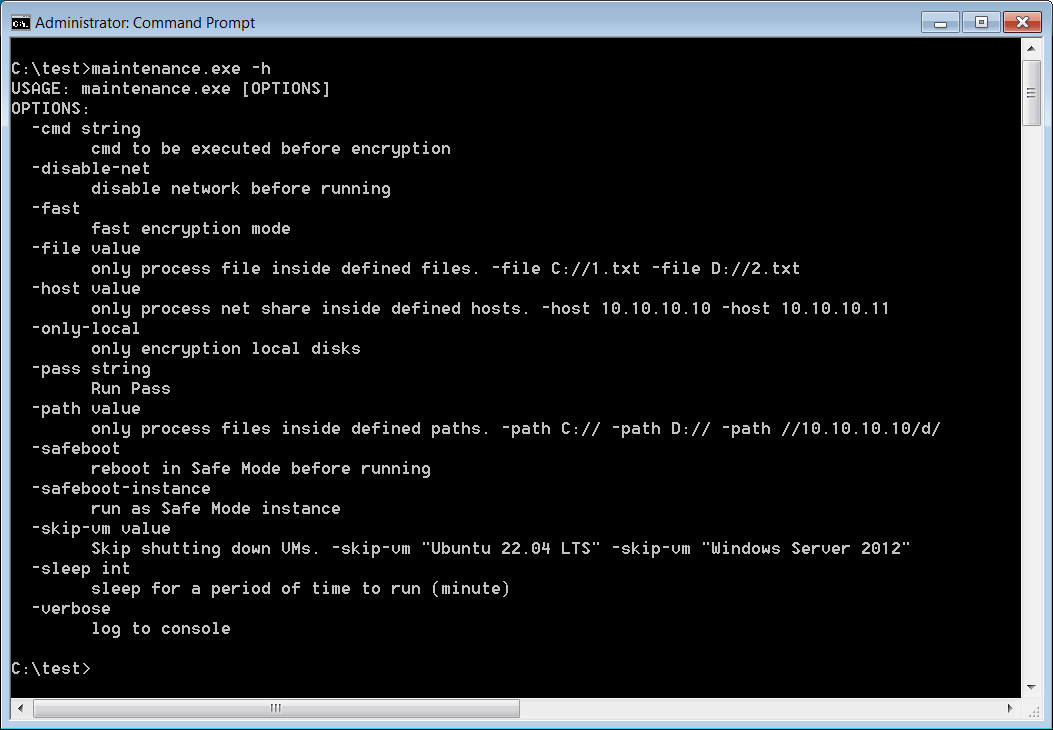
Supply: BleepingComputer
RansomHub
The RansomHub ransomware operation launched in February 2024, claiming it was an information theft extortion and extortion group that bought stolen recordsdata to the best bidder.
Nonetheless, quickly after, it was found that the operation additionally utilized ransomware encryptors in its double-extortion assaults, the place the risk actors breached networks, stole information, after which encrypted recordsdata.
The encrypted recordsdata and the risk to leak stolen information had been then used as leverage to scare firms into paying a ransom.
Symantec analyzed the ransomware encryptors and reported that they had been based mostly on the Knight ransomware encryptors, previously generally known as Cyclops.
The Knight operation claimed they bought their supply code in February 2024 and shut down simply as RansomHub launched. This has made many researchers imagine that RansomHub is a rebrand of the Knight ransomware operation.
Right now, the FBI launched an advisory about RansomHub, sharing the risk actor’s techniques and warning that they breached at the very least 210 victims since February.
It’s common for the FBI and CISA to publish coordinated advisories on risk actors quickly after they conduct a extremely impactful assault on important infrastructure, similar to Halliburton. Nonetheless, it isn’t identified if the advisory and the assault are linked.
For the reason that begin of the 12 months, RansomHub has been answerable for quite a few high-profile assaults, together with these on American not-for-profit credit score union Patelco, the Ceremony Help drugstore chain, the Christie’s public sale home, and U.S. telecom supplier Frontier Communications.
The ransomware operation’s information leak website was additionally utilized to leak stolen information belonging to Change Healthcare following the shutdown of the BlackCat and ALPHV ransomware operation.
It’s believed that after BlackCat shut down, a few of its associates moved to RansomHub, permitting them to shortly escalate their assaults with skilled ransomware risk actors.

