In 2017, a malicious actor exploited the alerts in Dallas’s emergency siren system and set off alarms for over 90 minutes. A majority of these assaults can have an effect on units that use radio frequency (RF) know-how, from sensible safety programs to plane. RF additionally performs a crucial position in lots of army programs equivalent to navigation, radar, and communication programs. Widespread DoD use circumstances embrace satellite tv for pc communication (SATCOM), radar, and tactical knowledge hyperlinks that assist coordinate troop actions, sign place details about a goal, or assist preserve communication between plane and drones. A current report indicated the DoD is inclined to potential RF assault vectors, indicating the necessity to higher perceive and stop vulnerabilities.
On this RF 101 information, we discover a few of the fundamentals of radio frequency communication, delve into the generalities of protocols and system interactions, focus on frequent RF instruments, and uncover methods malicious actors can assault programs. We summarize the fundamentals of RF know-how and the dangers related to it, and we focus on how the SEI helps to safe wi-fi communications.
RF Fundamentals
The electromagnetic spectrum covers your entire vary of electromagnetic waves from very lengthy radio waves to seen gentle to very brief, high-energy radiation equivalent to X-rays and gamma rays. The radio spectrum is a subset of the broader electromagnetic spectrum and ranges in frequency from 3 Hz to three,000 GHz. The power of RF waves to propagate, or journey via completely different mediums, together with the vacuum of area, allows wi-fi communication with out the necessity for bodily connection. RF alerts are basic to fashionable communication programs, which allow a lot of right now’s applied sciences together with tv, radio broadcasts, mobile communication, and Wi-Fi connections. Wi-fi RF communication additionally performs an important position in area domains, equivalent to satellite tv for pc communication to floor stations, which allow transmission of telemetry knowledge, GPS, and different alerts. The radio spectrum will be divided into standardized bands starting from extraordinarily low frequency (ELF) to tremendously excessive frequency (THF) as seen beneath.

Determine 1: The Electromagnetic Spectrum
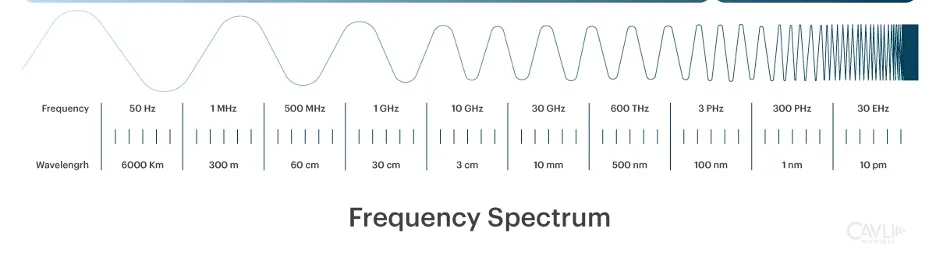
Determine 2: Frequency Spectrum
What Are Protocols and RF Modules?
RF modules are small digital units which can be used to transmit and obtain radio alerts between two units which can be bodily separated. Transmitters are answerable for transmitting radio waves that carry analog or digital info, and receivers obtain the radio waves and recuperate the data. That is the idea of a wi-fi communications channel, the open-space path via which info is transmitted by way of electromagnetic waves with out the usage of bodily connections equivalent to wires or cables. The general sign is constructed of the provider sign, a periodic waveform that conveys info by way of modulations that encode the analog or digital info. Modulation is the method of various a provider sign to encode knowledge then demodulating that acquired sign to decode knowledge. Modulation strategies decide how info is transmitted over radio waves, affecting the effectivity and high quality of communication.

Determine 3: Block Diagram of Digital Communication System
There are completely different ways in which the data will be modulated. Widespread analog modulations embrace amplitude modulation (AM) and frequency modulation (FM). AM modulates the next frequency provider with a decrease frequency sign by adjusting the amplitude of the provider sign. The frequency of the provider is unaltered, however the amplitude varies continuously. FM modulates by making comparatively small changes to the frequency of the provider. These two strategies characterize the sorts of RF alerts on the acquainted AM and FM radio bands. Widespread digital modulations, constructing on AM and FM, embrace amplitude shift keying (ASK) and frequency shift keying (FSK).
Inside a system, transmitters and receivers will be packaged collectively as transceivers, which carry out each capabilities. Moreover, system on a chip (SoC) configurations combine microcontrollers with the transceiver to permit protocol administration equivalent to knowledge packetization.

Determine 4: Illustration of Indicators
Communication protocols are units of guidelines for the alternate of data between the transmitter and receiver. They guarantee knowledge is transmitted in a constant format, permitting units from completely different producers to speak effectively in the event that they respect the protocol. There are numerous completely different sorts of protocols in use. Essentially the most immediately recognizable communication protocol for a lot of is mobile wi-fi.
Mobile wi-fi is the industrial driver of the digital wi-fi communication revolution. From its industrial introduction greater than 30 years in the past for cellular voice communication, digital wi-fi know-how has developed, extending the web to our cellular units. At a look:
The continued evolution of the world-wide mobile knowledge community is pushed by two organizations filling distinct however interconnected roles. The Worldwide Telecommunication Union (ITU), units the general necessities and pointers for worldwide cellular telecommunications (IMT) requirements. The third Era partnership Mission (3GPP), a world collaboration of business, requirements, and different organizations, performs research after which develops technical specs for cellular communication applied sciences. The ITU guides, evaluations, and approves 3GPP’s specs as worldwide requirements, guaranteeing they meet world necessities.
The 3GPP parallel examine and specification course of has maintained a cadence of a specification launch each one to 2 years since 1990. These embrace packet-switched knowledge, which gives “at all times on” connection, eliminating dial up and enhancing entry to e mail and internet providers. LTE Launch 8 applied an adaptation utilizing QPSK, 16QAM, and 64QAM modulation. Later releases included further modulations. A timeline of commercially recognizable releases is introduced within the desk beneath:
Yr | Launch | Identify | Options | Modulation / Entry | Downlink Knowledge Price (bits/sec) |
1992 | Phase1 | 2G / GSM | GSM Commercially Provided DCS-1800 | GMSK/TDMA | 9.6 okay |
1997 | 96 | 2G / GSM | Circuit Switched Consumer Knowledge | GMSK/TDMA | 14.4 okay |
1998 | 97 | 2.5G / GPRS | Packet Switched Consumer Knowledge | GMSK/TDMA | 56-114k |
1999 | 98 | 2.75G / EDGE | Enhanced GPRS | 8PSK/TDMA | 384 okay (max) |
2000 | 99 | 3G / UMTS | W-CDMA Interface | QPSK/W-CDMA | 384 okay |
2002 | 5 | 3G / UMTS | HSDPA | 16QAM/W-CDMA | 2-12 M |
2008 | 8 | 4G / LTE | LTE Launched | OFDMA | 5-100M |
2018 | 15 | 5G / NR | NR Launched | OFDMA | 100-1000M |
Some further incessantly used wi-fi protocols embrace:
- Wi-Fi: That is the acquainted wi-fi IEEE 802.11-based protocol that operates within the 2.4 GHz ISM Band with 14 channels spaced 5 MHz aside. In the US, channels 1 via 11 are generally used, particularly channels 1, 6 and 11, that are the one non-overlapping channels. Wi-Fi is utilized in properties, metropolis infrastructures, geolocation, industrial environments, and Web of Issues (IoT) functions.
- Bluetooth low power: That is the acquainted low-power protocol utilized by various units for close-proximity communication. It operates within the 2.4 GHz ISM Band. Frequency-hopping unfold spectrum (FHSS) is the modulation approach used, and its band is split into 40 2-MHz channels. It’s utilized in sensible dwelling units, healthcare functions, location-based providers, and extra.
- Zigbee: This low-power wi-fi mesh community protocol is underneath the IEEE 802.15.4 radio specification. It operates on the 868 MHz radio band in Europe, the 915 MHz radio band in North America and Australia, and globally at 2.4 GHz. It might probably transmit over a distance of as much as 100 meters (line of sight) and might obtain uncooked knowledge throughput charges as much as 500 kbps. Zigbee operates on 16 fastened channels which can be 5 MHz aside within the 2.4 GHz band. It’s primarily utilized in dwelling automation, sensible power, wi-fi sensing and industrial automation.

Determine 5: Wi-Fi and Zigbee Channels
How Do Units Talk with One One other?
Units talk by encoding knowledge into modulated alerts on a provider wave at a selected frequency. As seen in Determine 5, two Zigbee radios speaking on channel 19 can be speaking on the frequency of 2445 MHz.
Antennas are required in wi-fi communication since they’re answerable for radiating alerts into the air (i.e., transmitter) and receiving the incoming alerts (i.e., receiver). Antenna designs are decided by the character of the communication utility, the meant frequencies and modulation methodology, and high quality elements equivalent to vary, bandwidth, and working atmosphere.
Multiplexing is a technique that enables a number of transmitted alerts or streams of data to be shared over a single shared communication channel. Frequency division multiplexing permits a number of customers to ship knowledge via a single communication channel by dividing the overall channel into a number of sub-channels with non-overlapping provider frequencies. These sub-channels are allotted to separate customers or units. For instance, Zigbee, as famous above, operates on 16 channels within the 2.4 GHz vary. Time division multiplexing schemes assist handle entry to a channel by allocating particular person customers or units a selected timeslot for info transfers on the identical shared provider frequency to keep away from colliding transmissions. Customers or units transmit in speedy succession, every with their very own timeslot. There are additionally extra complicated approaches to multiplexing equivalent to code division multiplexing which use superior strategies like direct sequence unfold spectrum or frequency-hopping unfold spectrum to permit customers entry to your entire bandwidth for your entire length of transmission by assigning every system/person a singular, orthogonal code.
RF Assaults
RF assaults exploit vulnerabilities to intercept, disrupt, or manipulate programs and related protocols. The implications of RF assaults can vary from knowledge breaches and lack of confidentiality to denial of service and disruption of crucial communications. An instance that illustrates RF safety dangers is railroad and practice jacking, as within the current Poland railway assault stopped 20 trains in 2023. As wi-fi know-how grows, so do the assault discipline and threats.
What Are Widespread Forms of RF Assaults?
A number of frequent RF assault vectors exploit weaknesses in wi-fi communications. Widespread vectors embrace the next:
- Eavesdropping includes intercepting and listening to wi-fi communications with out authorization. This could permit a malicious actor to realize entry to delicate info equivalent to passwords, authentication processes, private info, or import system processes. Attackers can make the most of software-defined radios (SDRs) to seize and decode transmitted knowledge in a versatile method, enabling attackers to quickly adapt as they be taught extra about frequencies, modulation strategies, and protocols.
- Replay assaults, that are analogous to man-in-the-middle (MITM) assaults in cybersecurity, happen when an attacker captures legitimate transmissions after which retransmits them to impersonate a reputable system or person. These assaults can bypass authentication or achieve unauthorized entry to programs. For instance, a malicious actor might sniff the transmissions that carry the code from a wise lock to unlock/lock a door or sniff and replay the rolling code from a car’s key fob to acquire entrance to a automobile.
- Relay assaults improve a legitimate radio sign and use it to entry a legitimate goal. In contrast to a replay assault, which captures and resends the sign, a relay assault permits a sign to journey farther and be used at longer distances. Sensible fobs and keys are inclined to the sort of assault.
- Jamming is a denial-of-service assault the place the attacker transmits radio alerts on the identical frequency because the focused communication, successfully disrupting or blocking the reputable alerts. This could forestall units from speaking, which may result in service outages or operational disruptions.
RF Vulnerabilities
On this part, we analyze current examples of notable RF assaults which were written about within the public press.
Replay Assault
Keyless entry programs have modified how folks use automobile keys and entry safe areas, changing outdated bodily keys with key fobs. Nevertheless, these programs are weak to RF assaults. Automobile key fobs use RF alerts to ship a code to automobiles, permitting them to be unlocked and even began. From the late Nineteen Eighties to early 2000s, keyless entry programs emerged as a premium on plenty of automobiles. Like a storage door opener, a button can be pressed on the keyless entry system, transmitting an RF sign to the automobile, and a code would permit the automobile to be locked or unlocked. With little-to-no safety included of their preliminary design, early keyless entry programs have been weak to cloning and replay assaults. Because the know-how grew to become extra plentiful, safety elevated, including primary encryption to keyless entry units and options such because the rolling key methodology. Within the rolling key methodology, a brand new code is generated every time a button is pressed on the important thing fob. With the introduction of rolling keys, primary replay assaults not labored as a result of the captured and replayed code didn’t match the newly generated code.
In response to this stronger protection, two new forms of replay assaults emerged, the RollBack assault and the RollJam assault. RollBack captures two alerts: when a key’s pressed, the primary sign is jammed, and the second sign is allowed. The primary sign is then replayed, after which inside 5 seconds, the second sign is replayed to permit entry. Just like the RollBack assault, the RollJam assault captures two alerts. In contrast to RollBack, each alerts one and two are jammed, after which sign one is replayed rapidly, permitting the proprietor entry to the automobile. Then the second sign is replayed later by the attacker.

Determine 6: RollJam and RollBack Assaults on Keyless Automobile Methods
Automobile theft is a well-liked use of replay assaults. Nevertheless, dwelling automation programs may also be victims of these kinds of assaults. RF doorbell alerts will be cloned and replayed, as proven on this demonstration.
Relay Assault
Keyless entry programs are actually frequent options on most automobiles, and a brand new premium characteristic has emerged. With keyless automobile fobs, a sign from the important thing fob is at all times transmitting and the proprietor doesn’t have to hit a button to unlock the automobile. Just like the replay assault, relay assaults use a tool to seize a radio sign. As a substitute of copying the sign, the system boosts the sign to a second system to make it look like a key fob is close to the automobile. This assault normally requires two folks. The primary thief stands near the automobile, whereas the second thief is close to the home attempting to pay attention for the always-transmitted sign from the important thing fob. As soon as the second thief can get the sign from the important thing fob, they replay that sign to the primary thief. As soon as the primary thief is within the automobile, the second thief will relay one other sign to the primary thief, who’s now in a position to begin the automobile.

Determine 7: Instruments utilized in replay and relay assaults
Compounding the problem, all communication alerts that use radio frequency should register with the Federal Communication Fee (FCC). Key fobs have an FCC ID, which tells the frequency used. There are industrial instruments out there that permit an attacker to make use of the ID to set the frequency on their system, simplifying the method since they don’t have to make use of different instruments to scan RF alerts and decide the frequency.
Affiliation Flood Assault
In an affiliation flood assault, an attacker exploits the method by which a brand new Zigbee node joins a community. In a Zigbee community, there’s a coordinator (grasp of the community), a router, and endpoints. The assault begins when a malicious actor replicates the becoming a member of procedures, the place a brand new node sends a beacon request to the coordinator of the community, adopted by an affiliation request. By flooding the coordinator with quite a few faux requests, the attacker can overwhelm the community. This enables the malicious actor to realize unauthorized entry in a community of dwelling or workplace units to delicate knowledge, management units, or simply usually trigger disruptions to the Zigbee community.

Determine 8: Zigbee Mesh Community Topology
RF Vulnerabilities in Protection Functions
RF know-how is closely utilized in protection functions since superior radio know-how is used to hold out operations. Wi-fi communications have performed an integral position in tactical missions and normal warfare and protection operations. Safe alerts are used to guard voice and knowledge communications throughout operations. For instance, Single Channel Floor and Airborne Radio Methods (SINCGARS) are army programs that present voice and knowledge to command-and-control operations. There are military-specific GPS alerts which can be designed to withstand jamming and assist management the operational atmosphere. Spectrum utilization within the army area is a crucial a part of fashionable army operations that assist assist coordination and administration. Whether or not offering voice, knowledge, or cellular ad-hoc networking capabilities to warfighters, RF helps the monitoring of apparatus or automobiles or coordinating items with plane and drones. It’s a necessary device for battle planning.
Spoofing and Jamming in GPS and Radar Methods
GPS alerts, essential for navigation and sustaining dependable positioning knowledge for operations, are an integral part of army operations. Nevertheless, there was an increase of GPS assaults throughout the previous few years, as these programs will be spoofed or jammed by adversaries. Spoofing includes creating counterfeit alerts that may deceive receivers, equivalent to giving an incorrect location. GPS and radar programs are inclined to affiliation flood assaults, making your entire community consider there are extra legitimate nodes then there actually are. The confusion created can be utilized to mislead drones or unmanned aerial automobiles (UAV) to a fallacious vacation spot.
GPS spoofing in army operations is conceptually just like the automobile key fob assault described above. In a GPS spoofing assault, an adversary would possibly use ground-based programs to broadcast false GPS alerts that deceive army GPS receivers, main them to navigate to incorrect coordinates. Simply as a automobile will be tricked into accepting a replayed key fob sign, army programs counting on GPS will be misled by a replayed or faux sign. Equally, an adversary might use an RF jamming system to intrude with a radar system, stopping it from detecting incoming plane and deceptive radar operators into considering an incoming plane is coming from a distinct location.
In these circumstances, the vulnerability lies within the transmission of RF alerts with out correct safeguards towards interception, replay, or manipulation. Additional analysis into safeguarding and securing these programs towards dangers with extra anti-jamming strategies, superior encryptions, or different pathways will assist guarantee nationwide safety.
Work with the SEI
Understanding RF vulnerabilities and dangers is step one in studying the way to mitigate them. Right here on the SEI, we’re creating instruments and processes to securely harness the ability of RF. For instance, we’re creating machine studying (ML) strategies to foretell RF sign power and modulation varieties to assist speed up the aptitude of conventional physics-based modeling and simulation. This elevated velocity can allow functions at present not possible, equivalent to large-scale threat evaluation with uncertainty quantification, design optimization over very giant choice areas, and extra practical real-time war-gaming.
Moreover, the SEI is working to modernize present processes, knowledge, and digital infrastructure by creating software program instruments and knowledge pipelines that assist RF spectrum operations because the disciplines of wi-fi communications and conventional cybersecurity operations proceed to maneuver in the direction of convergence. In case you are fascinated about studying extra about this work or collaborating with the SEI, please contact us.

