
Menace actors more and more use Scalable Vector Graphics (SVG) attachments to show phishing types or deploy malware whereas evading detection.
Most photos on the internet are JPG or PNG recordsdata, that are product of grids of tiny squares known as pixels. Every pixel has a particular shade worth, and collectively, these pixels kind your complete picture.
SVG, or Scalable Vector Graphics, shows photos otherwise, as as a substitute of utilizing pixels, the pictures are created via strains, shapes, and textual content described in textual mathematical formulation within the code.
For instance, the next textual content will create a rectangle, a circle, a hyperlink, and a few textual content:
<svg width="200" top="200" xmlns="http://www.w3.org/2000/svg">
<!-- A rectangle -->
<rect x="10" y="10" width="100" top="50" fill="blue" stroke="black" stroke-width="2" />
<!-- A circle -->
<circle cx="160" cy="40" r="40" fill="crimson" />
<!-- A line -->
<line x1="10" y1="100" x2="200" y2="100" stroke="inexperienced" stroke-width="3" />
<!-- A textual content -->
<textual content x="50" y="130" font-size="20" fill="black">Hiya, SVG!</textual content>
</svg>When opened in a browser, the file will generate the graphics described by the textual content above.

Supply: BleepingComputer
As these are vector photos, they mechanically resize with out shedding any loss to picture high quality or the form, making them perfect to be used in browser functions that will have totally different resolutions.
Utilizing SVG attachments to evade detection
Using SVG attachments in phishing campaigns is nothing new, with BleepingComputer reporting about their utilization in earlier Qbot malware campaigns and as a approach to cover malicious scripts.
Nonetheless, risk actors are more and more utilizing SVG recordsdata of their phishing campaigns in response to safety researcher MalwareHunterTeam, who shared latest samples [1, 2] with BleepingComputer.
These samples, and others seen by BleepingComputer, illustrate how versatile SVG attachments will be as they not solely mean you can show graphics however may also be used to show HTML, utilizing the <foreignObject> factor, and execute JavaScript when the graphic is loaded.
This enables risk actors to create SVG attachments that not solely show photos but in addition create phishing types to steal credentials.
As proven beneath, a latest SVG attachment [VirusTotal] shows a faux Excel spreadsheet with a built-in login kind, that when submitted, sends the info to the risk actors.
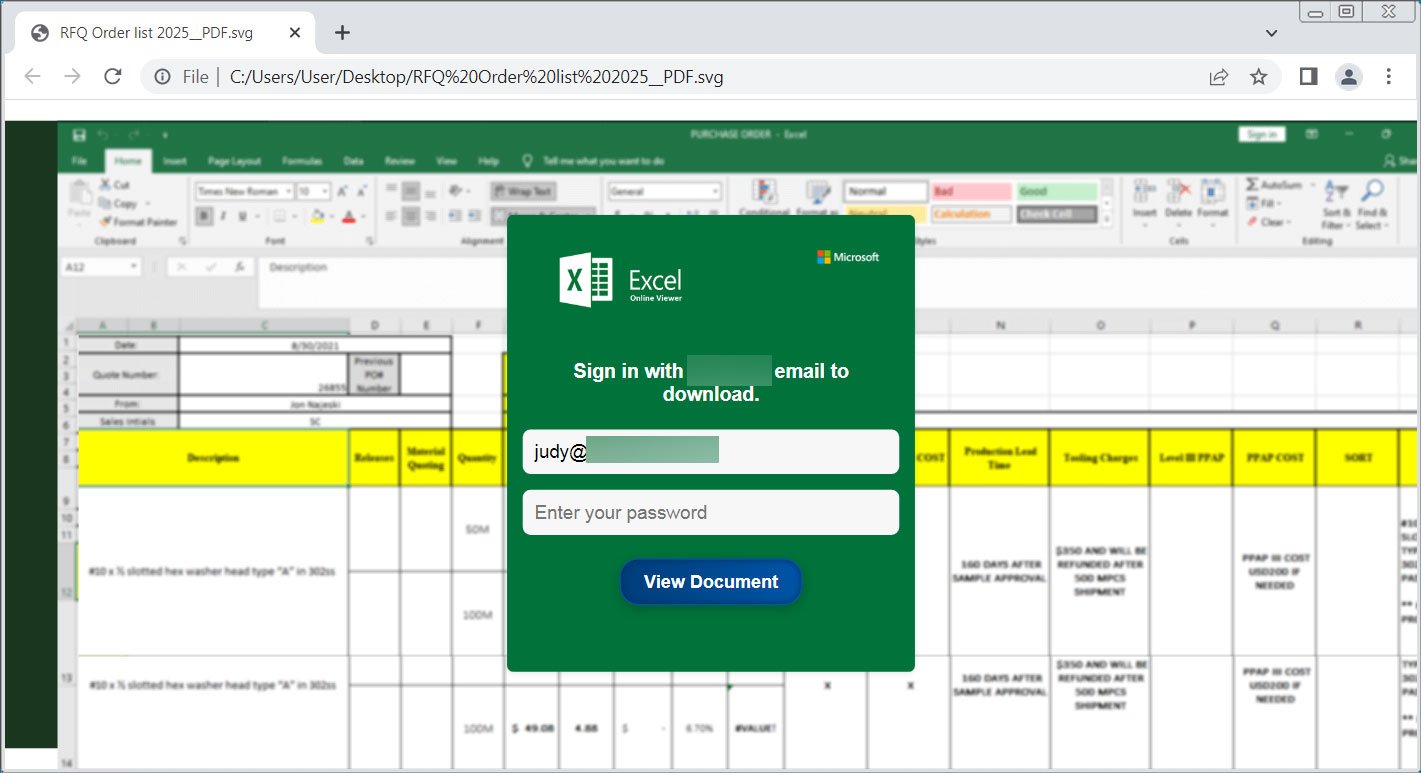
Supply: BleepingComputer
Different SVG attachments utilized in a latest marketing campaign [VirusTotal] faux to be official paperwork or requests for extra data, prompting you to click on the obtain button, which then downloads malware from a distant website.
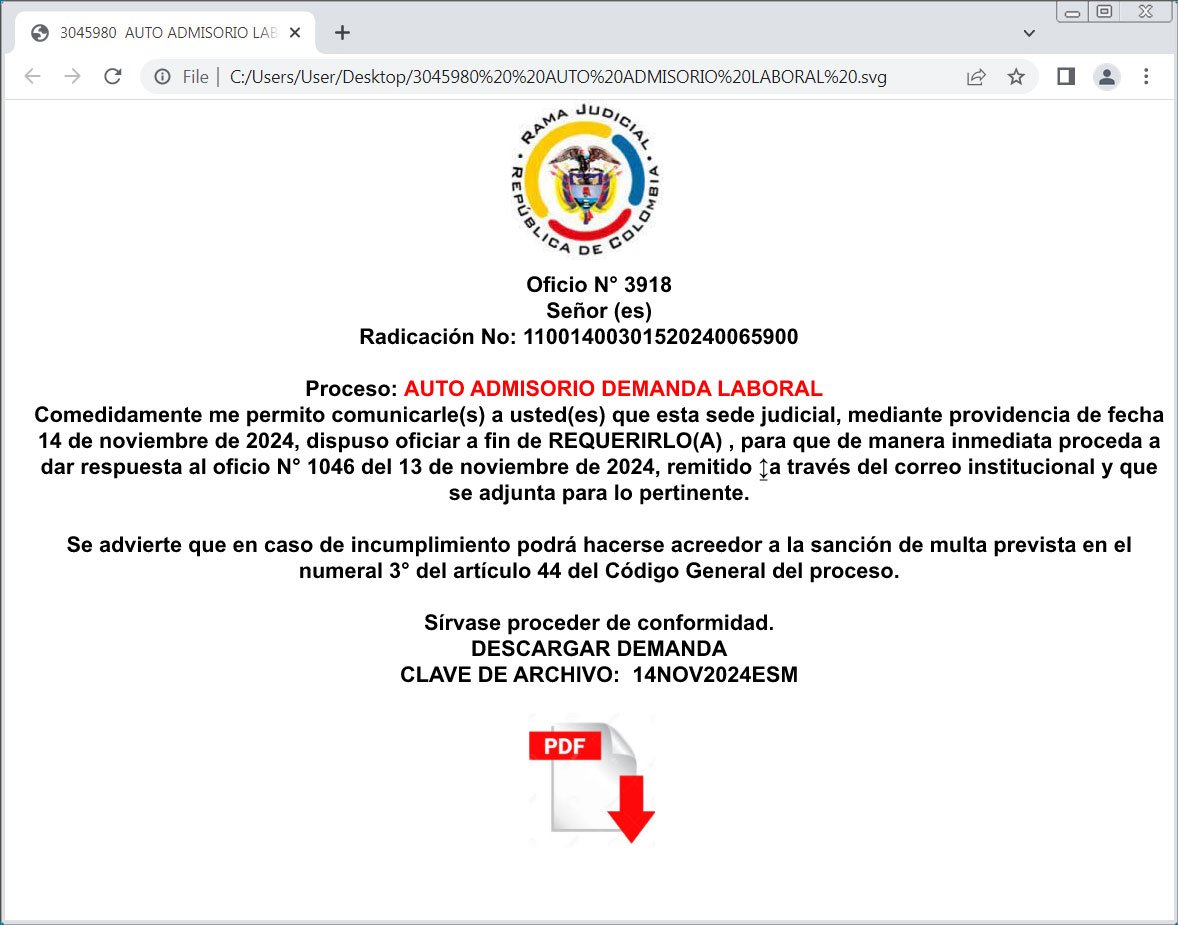
Supply: BleepingComputer
Different campaigns make the most of SVG attachments and embedded JavaScript to mechanically redirect browsers to websites internet hosting phishing types when the picture is opened.
The issue is that since these recordsdata are largely simply textual representations of photos, they have an inclination to not be detected by safety software program that usually. From samples seen by BleepingComputer and uploaded to VirusTotal, on the most, they’ve one or two detections by safety software program.
With that stated, receiving an SVG attachment will not be widespread for reliable emails, and may instantly be handled with suspicion.
Except you’re a developer and count on to obtain these kinds of attachments, it’s safer to delete any emails containing them.

